by titanadmin | May 26, 2016 | Email Scams, Phishing & Email Spam, Spam News |
With 1.65 billion active Facebook accounts, the social media network is a big target for scammers, so it is no surprise that there is a new Facebook phishing scam currently doing the rounds. If the spammers behind the latest attacks can get even a tiny percentage of users to fall for the scam they could be in for a very big payday.
Latest Facebook Phishing Scam Warns of Violation of Terms of Service
The latest Facebook phishing scam threatens account holders by telling them that their accounts will be closed due to a violation of Facebook’s terms of service. The email claims that the account owner has been reported for irregularities of content and that action must be taken to correct the issue of the account will be permanently closed.
The message contains an ow.ly shortlink that users must click to verify that they are the actual owner of the account. The link contains the works “Verify” and “Facebook,” which may fool some message recipients into thinking the message is genuine.
The link included in the email is fake of course. It directs the victim to a phishing website where they are asked to supply their login credentials. If account holders are fooled into clicking the link they are likely to proceed and enter in their account login and password, which will not grant access to Facebook to remove the offending violations. It will simply give those credentials to the attackers. Victims are also asked to supply their date of birth and a security question.
Since many people often use the same passwords for multiple social media accounts, email accounts, and online banking, the potential losses could be considerable. Worse still, many individuals use the same passwords for their private accounts as they do for their work accounts. The fallout from this single scam could therefore be considerable.
With the login and password, the attackers could abuse the account and use it to send phishing messages to all of the account holder’s friends. However, the latest scam does not stop there. After supplying these details, the second phase of the scam starts. The victim is directed to a new page where they are asked for their credit card details to confirm their identity. If supplied, the details would be used to make purchases in the victim’s name
This latest Facebook phishing scam is fairly easy to spot as it contains many tell-tale signs that the notification is not real. The message starts with “Dear Customer” for a start. It would be reasonable to assume that Facebook would know the account holder’s name and would address the email to them personally. Not that Facebook sends out email notifications such as this, although many users would be unaware of that. The message also uses poor grammar, and an ow.ly link rather than a facebook.com hyperlink.
Suspected Page Forgery Facebook Scam Email Targets Business Users
Another version of this scam uses the same format as Facebook notifications sent to account holders via email. This email is harder to identify as a Facebook phishing scam. The link supplied appears to be a genuine Facebook link and the address supplied in the email also appear to be genuine. Correct English is used and the email has been very carefully crafted.
Clicking the link will take the user to a webpage that uses the Facebook logo and color scheme. The page explains there has been a violation of Facebook’s Terms of Service and that an unacceptable offer has been made using Facebook’s offer creation tool. Users are asked to secure their account if this is a mistake. To secure the account users must enter their username and password, and set a new security question. As with the other version, the account details will be used to hijack the account.
All Facebook users – businesses and individuals – should be particularly wary about Facebook emails and be wary of scams. If any Facebook messages are received, the account should be checked by logging in via the browser or using the Facebook App, never using the link supplied in the email. If there is a problem with the account, users will be informed of this when they login.
by titanadmin | May 20, 2016 | Email Scams, Industry News, Phishing & Email Spam, Spam Advice, Spam News |
According to a recent report on spam email from anti-virus software developer Kaspersky Lab, the decline in spam email over the past few years appears to have reversed, with the first quarter of 2016 seeing a major increase in malicious spam email volume.
Major Increase in Malicious Spam Email Volume Reported by Kaspersky Lab
Over the past few years there has been a decline in the number of spam emails, as cybercriminals have sought other ways to deliver malware and defraud computer users. In 2015, the volume of spam emails being sent fell to a 12-year low. Spam email volume fell below 50% for the first time since 2003.
In June 2015, the volume of spam emails dropped to 49.7% and in July 2015 the figures fell further still to 46.4%, according to anti-virus software developer Symantec. The decline was attributed to the taking down of major botnets responsible for sending spam emails in the billions.
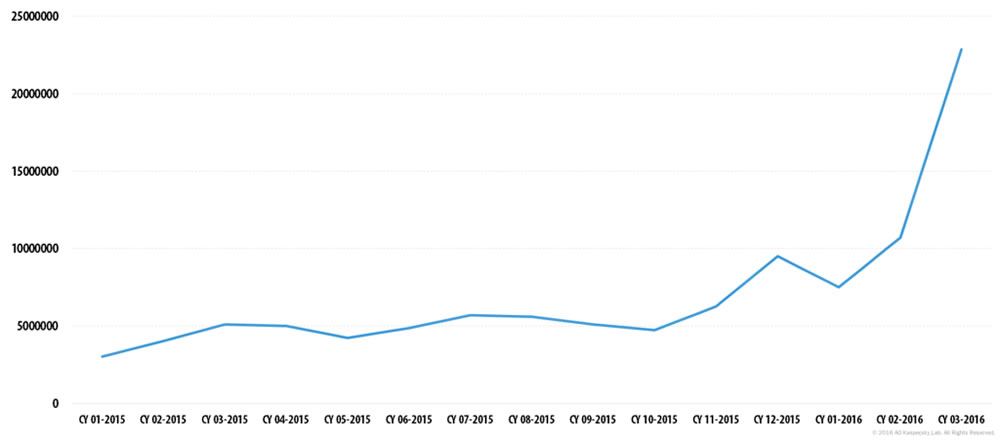
Malicious spam email volume has remained fairly constant during 2015. Between 3 million and 6 million malicious spam emails were detected by Kaspersky Lab throughout 2015; however, toward the end of the year, malicious spam email volume increased. That trend has continued in 2016.
Kaspersky Lab figures show that spam email messages containing malicious attachments – malware, ransomware, malicious macros, and JavaScript – started to increase in December 2015. That rise has continued, and in March 2016 malicious spam email volume had risen to four times the level seen in 2015. In March, 2016, Kaspersky Lab detected 22,890,956 malicious spam emails. Spam email volume as a whole increased over the quarter, rising to an average of 56.92% for the first three months of 2016.
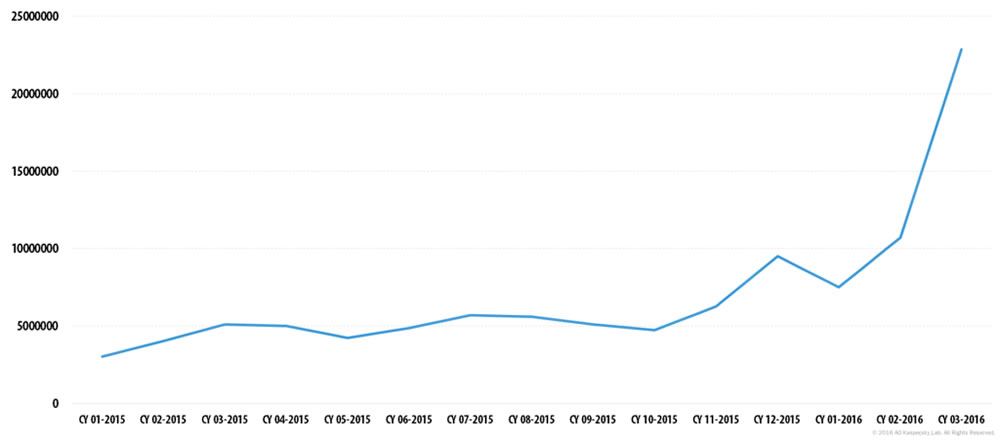
Image source: Kasperky Lab
Wide Range of Malicious Files Being Sent in Spam Email
While it was common for virus-loaded executable files to be sent as email attachments, these are now commonly caught by email filters and are marked as spam. However, spammers have been developing new methods of getting past traditional webmail spam filters. The spam emails intercepted by Kaspersky Lab now contained a wide variety of malicious files.
One of the most common methods now used by spammers is to send office documents infected with malicious macros. Microsoft Word files with the extension DOC and DOCX are commonly used, as are rich text format files RTF, Adobe PDF files, and Microsoft Excel spreadsheets with the extensions XLS and XLSX.
These file formats are commonly opened as many end users are less suspicious of office documents than they are about ZIP, RAR, and EXE files. Most office workers would know not to open a EXE file that was emailed to them by a stranger, yet an office document – a file format they use on a daily basis – is less likely to arouse suspicion.
Instead of the emails containing the actual malware, virus, or ransomware payload, they contain Trojan downloaders that download JS scripts. Those scripts then perform the final stage of infection and download the actual malware or ransomware. This method of attack is used to bypass anti-virus protections.
Web Filters and Email Spam Filters Should be Used to Reduce the Risk of a Malware Infection
There has been an increase in drive-by downloads in recent years as attackers have lured victims to websites containing exploit kits that probe for vulnerabilities in browsers and browser plugins. Visitors are redirected to these malicious websites when visiting compromised webpages, via malvertising, and malicious social media posts. While drive-by downloads are still a major threat, the use of web filters and anti-virus software browser add-ons are blocking these malware downloads and malicious websites.
Email is still a highly effective way of getting past security defenses and getting end users to install malware on their devices. Carefully crafted emails that include unique text increase the likelihood of the scammers getting users to open malicious attachments. Oftentimes, the messages include personal information about the recipient such as their name or address. This has helped the spammers to get the victims to take the desired action and run malicious macros and install malware.
It may be too early to tell whether spam email volume has only temporarily spiked or if there is a reversal in the decline of spam, but organizations and individuals should remain vigilant. The increase in malicious spam email volume should not be ignored.
Staff members should receive regular training on how to identify malicious email messages and phishing scams. It is also a wise precaution to use a robust spam filter such as SpamTitan. SpamTitan blocks 99.97% of malicious spam email messages, dramatically reducing the probability of malware, ransomware, adware, and spyware being installed.
by titanadmin | May 12, 2016 | Email Scams, Phishing & Email Spam, Spam Advice, Spam News |
Scammers are constantly coming up with crafty ways to fool computer users into revealing login credentials and installing malware, with the latest speeding ticket email scam being used for the latter. Emails are being sent to individuals claiming they have been caught driving too fast and are sent a link to click to pay their speeding ticket.
If the targeted individual clicks on the link contained in the spam email they will be directed to a malicious website that will download malware onto their computer.
This particular scam has been used to target drivers in Philadelphia. While the majority of spam emails are sent out randomly in the millions in the hope of fooling some individuals into clicking on malicious links, this particular campaign is anything but random. Individuals are being targeted that are known to have exceed the speed limit.
Not only have the attackers obtained the email addresses of their targets, they have also send details of where the individual exceeded the speed limit. So how is this possible?
This particular speeding ticket email scam is understood to have been made possible by the attackers hacking a Smartphone app that has access to the GPS on the phone. The attackers use location data and the phones GPS to determine which individuals have exceeded the speed limit. They are then sent a speeding ticket scam email telling them to click on a link where they can see details of their vehicle license plate in the location where the infraction took place. They are also informed of the speed limit in that location together with speed that the individual was travelling. The speeding driver is told he or she has 5 days to pay the citation.
While this speeding ticket email scam could easily be used by the attackers to obtain credit card details or phish for other information, it appears to only be used to install malware. Clicking on the link in the email to view license plate details does not actually reveal the image. It silently installs malware.
The police department in Tredyffrin, PA, where drivers were targeted with this speeding ticket email scam, has not cited callers for their speeding violations when they have called to query the fine, even when they have confessed to speeding over the phone.
How to Protect Yourself Against Email Scams
This speeding ticket email scam is particularly convincing as it uses real data to fool users into clicking on the malicious link. Many spam email campaigns now use personal information – such as real names and addresses – to fool targets into opening infected email attachments or clicking on malicious links. This type of targeted spear phishing email is now all too common.
To protect against attacks such as this, there are a number of steps that should be taken.
- If contacted by email and asked to click a link, pay a fine, or open an attachment, assume it is a scam. Try to contact the individual or company to confirm, but do not use the contact information in the email. Perform a search on Google to obtain the correct telephone number to call.
- Carefully check the sender’s email. Does it look like it is genuine?
- Never open email attachments from someone you do not know
- If you receive an email offering you a prize or refund, stay safe and delete the email
- Ensure that anti-virus software is installed on your computer and is up to date.
by titanadmin | May 9, 2016 | Email Scams, Internet Security, Phishing & Email Spam |
File-encrypting ransomware is now one of the main UK cybersecurity threats. Rather than stealing sensitive corporate data, criminals have taken to locking it with powerful encryption to prevent businesses from performing day to day functions. Without access to data, business often grinds to a halt.
Ransomware is nothing new, but over the past few years it has become much more popular with cybercriminals who are increasingly targeting businesses. If criminals can succeed in breaching businesses’ security defenses and locking critical files, a ransom can be demanded in order to supply security keys to unlock the encryption. If no viable backup copy exists, businesses may be left with no alternative but to give in to attackers’ demands. Those demands include sizable payments in Bitcoin – A virtually anonymous currency.
Ransomware attacks in the United States have attracted the headlines, but across the pond, ransomware attacks on UK businesses have also been increasing. According to the latest research from ESET, ransomware is now one of the main UK cybersecurity threats accounting for more than a quarter of threats. In the week of April 19 to 26, 26.16% of threats involved ransomware.
How to Block Ransomware Infections
Unfortunately, there is no single method of blocking ransomware infections that is 100% effective, although by using a multi-layered approach, small to medium-sized businesses can greatly reduce the probability of ransomware being installed on their computers and networks.
Ransomware is installed via a number of different methods, although one of the most common methods of ransomware delivery is spam email. Spam email is used to send out malicious attachments that install malware, which in turn installs ransomware on computers. One of the most common methods of infection is Word documents containing malicious macros.
Attackers also use emails containing malicious links. End users are enticed to click those links using social engineering techniques. One click is often all that is required to install ransomware. While it is possible to train employees to be more security aware, all it takes is for one member of staff to install malware for a network to be encrypted. The latest strains of ransomware are capable of encrypting files on single computers, connected USB drives, and network drives. It is important to provide staff training, but a software solution should also be used to block spam emails and prevent them from being delivered.
SpamTitan can keep an organization well protected from malware and ransomware infections. SpamTitan uses two leading anti-virus engines – Bitdefender and ClamAV – to block the vast majority of spam email. SpamTitan detects and blocks 99.98% of spam email, which prevents end users’ spam and phishing email detection skills from being put to the test.
SpamTitan blocks malicious emails, infected email attachments, and links to phishing websites and sites where drive-by downloads of malware take place. This single software solution can help organization mitigate the risk from many of the main UK cybersecurity threats.
If you want to block ransomware and malware and reduce the time your employees spend sifting through spam email, contact the sales team today for further information or sign up for a free SpamTitan trial.