In this article we explore the cost of HIPAA noncompliance for healthcare organizations, including the financial penalties and data breach costs, and one of the most important technologies to deploy to prevent healthcare data breaches.
The Health Insurance Portability and Accountability Act (HIPAA)
In the United States, healthcare organizations that transmit health information electronically are required to comply with the Health Insurance Portability and Accountability Act (HIPAA). HIPAA was introduced in 1996 with the primary aim of improving healthcare coverage for employees between jobs, although it has since been expanded to include many privacy and security provisions following the introduction of the HIPAA Privacy and Security Rules.
These rules require HIPAA-covered entities – health plans, healthcare providers, healthcare clearinghouses and business associates – to implement a range of safeguards to ensure the confidentiality, integrity, and availability of protected health information (PHI). Those safeguards include protections for stored PHI and PHI in transit.
HIPAA is not technology specific, if that were the case, the legislation would need to be frequently updated to include new protections and the removal of outdated technologies that are discovered not to be as secure as was initially thought. Instead, HIPAA leaves the actual technologies to the discretion of each covered entity.
In order to determine what technologies are required to keep PHI secure, covered entities must first conduct a risk analysis: A comprehensive, organization-wide analysis of all risks to the confidentiality, integrity, and availability of PHI. All risks identified must be managed and reduced to an appropriate and acceptable level.
The risk analysis is one of the most common areas where healthcare organizations fall afoul of HIPAA Rules. Healthcare organizations have been discovered not to have included all systems, hardware and software in the risk analysis, or fail to conduct the analysis on the entire organization. Vulnerabilities are missed and gaps remain in security controls. Those gaps allow hackers to take advantage and gain access to computers, servers, and databases.
When vulnerabilities are exploited, and a data breach occurs, HIPAA-covered entities must report the security breach to the Department of Health and Human Services’ Office for Civil Rights (OCR): The main enforcer of HIPAA Rules. OCR investigates data breaches to determine whether they could realistically have been prevented and if HIPAA Rules have been violated.
What is the Cost of HIPAA Noncompliance?
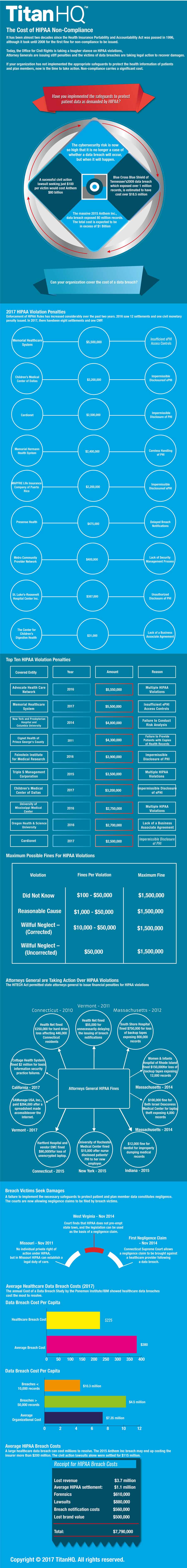
When healthcare organizations are discovered not to have complied with HIPAA Rules, financial penalties are often issued. Fines of up to $1.5 million per violation category (per year that the violation has been allowed to persist) can be issued by OCR. The cost of HIPAA noncompliance can therefore be severe. Multi-million-dollar fines can, and are, issued.
The cost of HIPAA noncompliance is far more than any financial penalty issued by OCR, or state attorneys general, who are also permitted to issue fines for noncompliance. HIPAA requires covered entities to notify individuals impacted by a data breach. The breach notification costs can be considerable if the breach has impacted hundreds of thousands of patients. Each patient will need to be notified by mail. If Social Security numbers or other highly sensitive information is exposed, identity theft protection services should be offered to all breach victims.
Forensic investigations must be conducted to determine how access to data was gained, and to establish whether all malware and backdoors have been removed. Security must then be enhanced to prevent similar breaches from occurring in the future.
A data breach often sees multiple lawsuits filed by the victims, who seek damages for the exposure of their information. Data breaches have a major negative impact on brand image and increase patient churn rate. Patients often switch providers after their sensitive information is stolen.
On average, a data breach of less than 50,000 records costs $4.5 million to resolve according to the Ponemon Institute and has an average organizational cost of $7.35 million.
The 78.8 million-record breach experienced by Anthem Inc. in 2015 is expected to have cost the insurer upwards of $200 million. That figure does not include lost brand value and reputation damage, and neither a HIPAA fine from OCR.
A summary of the cost of HIPAA noncompliance, including recent fines issued by attorneys general and OCR has been detailed in the infographic below.
The Importance of Protecting Email Accounts
There are many ways that unauthorized individuals can gain access to protected health information – via remote desktop applications, by exploiting vulnerabilities that have not been patched, accessing databases that have been left exposed on the Internet, or when devices containing unencrypted PHI are stolen. However, the biggest single threat to healthcare data comes from phishing.
Research from PhishMe indicates more than 90% of data breaches start with a phishing email, and a recent HIMSS Analytics survey confirmed that phishing is the biggest threat, with email ranked as the most likely source of a healthcare data breach.
Protecting email accounts is therefore an essential part of HIPAA compliance. OCR has already fined healthcare organizations for data breaches that have resulted from phishing emails.
Healthcare organizations should implement a solution that blocks malicious emails and scans for malware and ransomware. In addition to technology, employees must also be trained how to identify malicious emails and taught to be more security aware.
How TitanHQ Can Help with HIPAA Compliance
TitanHQ developed SpamTitan to keep inboxes secure and prevent email spam, phishing messages, and malware from being delivered to inboxes. SpamTitan blocks more than 99.9% of spam email, and dual anti-virus engines ensure emails with malicious attachments are identified and quarantined. With SpamTitan, your organization’s email accounts will be protected – an essential part of HIPAA compliance.
WebTitan compliments SpamTitan and offers an additional layer of protection. WebTitan is a web filtering solution that allows you to carefully control the websites that your employees visit. WebTitan will prevent employees from visiting malicious websites via emailed hyperlinks, general web browsing, malvertising or redirects, protecting your organization from web-based attacks, drive by downloads of ransomware and malware, and exploit kit attacks.
For more information on TitanHQ’s cybersecurity solutions for healthcare, contact the TitanHQ team today.