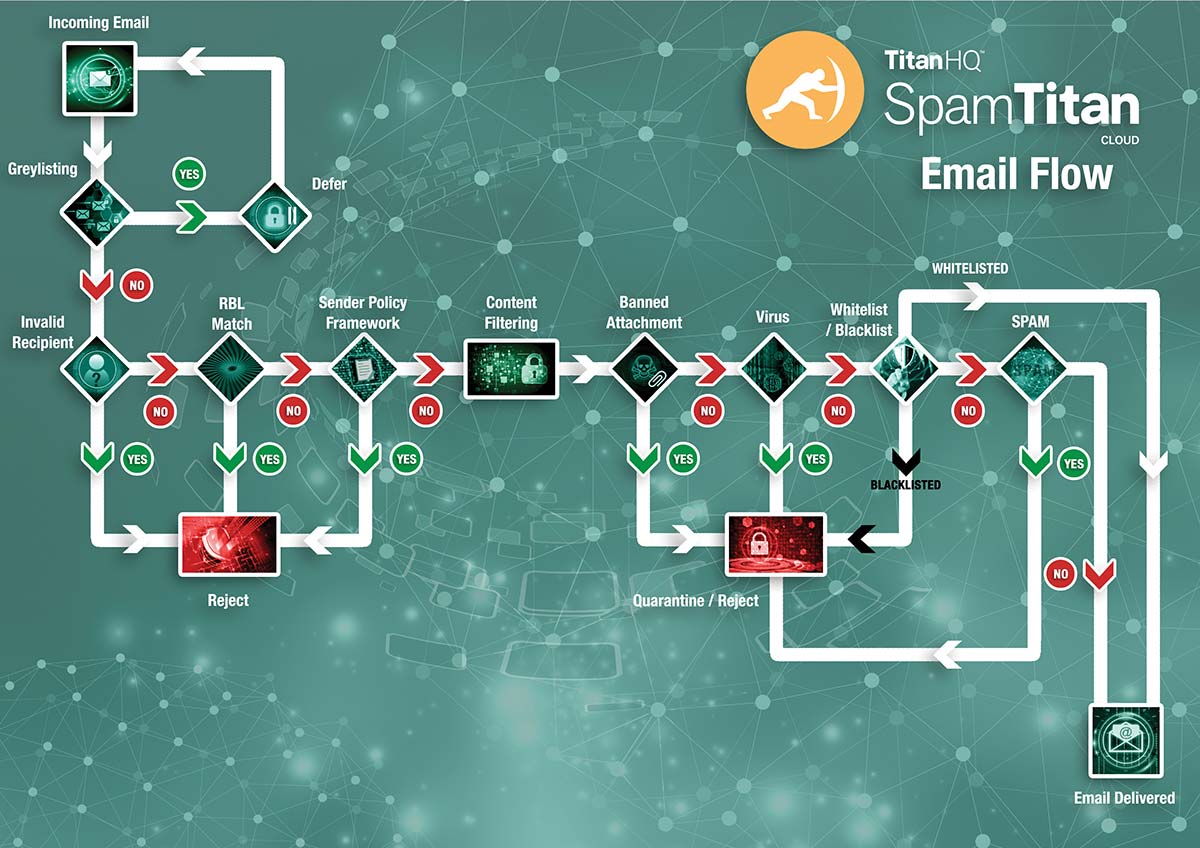
Back in the mid-1990s, Dave Rand and Paul Vixie – two software engineers who had significant roles to play in the development of the Domain Name System – developed the first type of anti-spam appliance. Originally no more a list of IP addresses from which spam had originated, Rand and Vixie shared the list with network managers via a DNS-based distribution method.
The distribution method was subsequently automated and developed into a Border Gateway Protocol, which later became the backbone of the “Mail Abuse Prevention System”. The list became known as the “Real-Time Blackhole List” and, more than twenty years later, it is still the primary mechanism for detecting spam emails in the majority of standard anti-spam appliances.
Real-Time Blackhole Lists have gone through some refinements in the past twenty years. RBL agencies can now assign Reputation Scores to IP addresses, which are added to the scores assigned by Content Analysis Tools to determine the “spam score” of incoming emails. If a spam score exceeds the anti-spam appliance´s “Spam Acceptance Threshold”, the email is quarantined, flagged or rejected.
Other Functions of Standard Anti Spam Appliances
Also over the past twenty years, the volume of spam email has increased and spammers´ techniques for evading detection have become more sophisticated. Anti spam appliances have kept pace with the increase in traffic and sophistication, and now include front-end tests such as Recipient Verification Protocols and Sender Policy Frameworks.
These two front end tests check recipient addresses to ensure they are valid, and reject emails from senders that have hidden their true identity behind a “spoofed” email address. By rejecting suspect emails before they are checked by a Real-Time Blackhole List and are assigned a spam score, anti spam appliances reduce the strain on the mail server.
Nonetheless, some spam emails still evade detection. Although a small percentage in the overall scheme of things, the spam emails that avoid detection are likely to be those that are most sophisticated and present the greatest threat. It is possible to counter threats by increasing the appliance´s “Spam Acceptance Threshold”, but this can result in genuine emails being classed as spam and rejected.
The Latest Generation of Spam Filter Appliances
The latest generation of spam filter appliances have more front end tests and more spam detection mechanisms than standard anti spam appliances. Depending on how they are configured, the latest generation of spam filter appliances can detect up to 99.97% of spam emails, compared to a typical spam detection rate of 97%-98% for standard anti spam appliances.
The key to achieving such a high detection rate is a process known as “Greylisting”. In the Greylisting process, every incoming email is returned to the mail server from which it originated with a request for the email to be resent. Spammers´ servers are usually too busy sending spam emails to reply to the request, and the spam email is never returned.
This process has both advantages and disadvantages. The primary advantage is that the delivery of spam emails from “not-previously-known-sources” is prevented as well as the delivery of spam emails from “previously-known-sources” as identified by the Real-Time Blackhole List. A second advantage is that Greylisting is a front end test and therefore further reduces the strain on the mail server.
The primary disadvantage of Greylisting is that it can delay the delivery of business-critical incoming emails. Although it is possible to “whitelist” specific senders in order to circumnavigate the Greylisting and filtering processes, whitelisting can be a gateway for spammers who have compromised a trusted email account or who are using botnets to send spam from sources with good IP reputations.
Did You Know?
99.99%
SpamTitan’s spam catch rate
11 Seconds
a ransomware attack occurs
$285
the average cost to manage spam per person without an email filter
56.50%
of all email is spam
Other Features in New-Gen Spam Filter Appliances
Other features in next-gen spam filter appliances not only help achieve higher spam detection rates and mitigate the risk from email borne threats, but also help with the administration of the appliance in order to lessen the maintenance overhead for system administrators and IT departments. These features include:
- SMTP Controls that can be configured to authenticate the sources of incoming emails.
- SURBL and URIBL filters that identify links to phishing and compromised websites.
- Antivirus software capable of identifying malware hidden in email attachments.
- Automatic software updates, RBL updates and SURBL/URIBL updates.
- Integration with backend management software such as AD and LDAP.
This final feature is particularly helpful for applying different “Acceptable Spam Thresholds” for different departments. For example, you may want to apply a higher threshold for your Finance Department than your Sales Department in order to offer a higher level of protection for your Finance Department without blocking potential leads being delivered to your Sales Department.
The Importance of Scanning Outbound Email
Inasmuch as scanning incoming emails is important to prevent spam and mitigate the risk from email borne threats, the importance of scanning outgoing emails should not be overlooked. If an outgoing email is considered by a Content Analysis Tool to contain spam, it will reflect badly on your business´s IP address. If this scenario happens too frequently, your IP address could be blacklisted by RBL agencies.
The consequences of having your business´s IP address blacklisted will not only affect your email communications. If your website uses the same IP address as your mail server, Internet filters may prevent visitors accessing the website. Although a problem with an IP address can be rectified within a couple of days, the damage to your business reputation may take longer to repair.
Scanning outgoing emails serves three functions. It can identify emails that have inadvertently been composed with too much content considered spammy (not a good idea in any business communication), identify email accounts compromised by botnets (which can also be used to launch DDoS attacks) and identify viruses and other infections your regular antivirus software may not yet have found.
The Three Different Types of Anti-Spam Appliance
The three different types of anti-spam appliance are hardware, software and cloud-based – a cloud-based anti-spam appliance often being referred to as an anti spam virtual appliance. They each have a place in the market depending on the size of your business, the nature of your business and the volume of traffic passing through your network.
A hardware anti-spam appliance generally suits very small businesses that uses alternative methods for the exchange of confidential information. Although a capital expenses rather than an operating expense, you may still find you need a service contract for software updates to make sure you protect computer systems from the latest malware, ransomware and phishing attacks.
A software anti-spam appliance is most suitable for businesses maintaining confidential information on premise who do not want confidential information travelling through the cloud. These appliances are normally installed as Gateway appliances between the firewall and the mail server and updated automatically by the service provider.
An anti spam virtual appliance is an ideal solution for business with significant network traffic, as the filtering processes are performed “off-network”. All that is required to implement an anti spam virtual appliance is a redirection of the MX server record, making it the easiest type of anti-spam appliance to deploy. As anti spam virtual appliances are multi-tenanted, they are also ideal solutions for MSPs.
Hear from our customers
The Cost of an Anti-Spam Appliance
The cost of an anti spam appliance varies considerably depending on the type of type of anti-spam appliance you want and the number of mailboxes you want to protect. Hardware appliances cost from a couple of hundred dollars up to tens of thousands. The more expensive ones are typically more complicated to use, without necessarily providing a higher level of protection.
With a software and virtual appliances, it is possible to get discounts on the cost of the license by paying in advance for the filtering service. We strongly recommend taking a free trial of the appliance in your own environment before committing to an advance payment. This will help you evaluate the appliance´s effectiveness, compatibility and ease-of-use.
You can find out the exact cost of a software anti-spam appliance and an anti spam virtual appliance by taking advantage of our “Instant Quote Calculator”. However, before you navigate away from this page, we would like to reinforce the cost of not implementing an anti-spam appliance:
| The Cost of Not Implementing an Anti-Spam Appliance | |
|---|---|
| Productivity Loss | Based on the number of hours an office worker spends managing spam emails, it costs businesses $285 per employee per year in productivity loss. |
| Malware & Viruses | The cost of not implementing an anti-spam appliance when malware and viruses evade detection can run into millions of dollars. |
| Ransomware | Recovering from a successful ransomware attack can cost more than any ransom paid. In 2017 the median “cost of recovery” was $133,000. |
| Phishing Attacks | Based only on the phishing attacks reported to them, the FBI estimates phishing costs US businesses more than $500 million each year. |
| Loss of Reputation | As mentioned previously, damage to an IP address can be rectified within a couple of days. Repairing your business reputation may take longer. |
SpamTitan´s Spam Filter Appliances
SpamTitan´s spam filter appliances have been developed to be as versatile and scalable as your business needs. We offer the choice of a software anti-spam appliance or an anti spam virtual appliance – depending on your specific requirements – both of which are capable of achieving a verifiable spam detection rate of 99.97%.
Both types of anti spam appliance offer businesses the choice of how they want spam email to be handled. Both have the option of Greylisting and scan outgoing emails by default. All the features mentioned in our new-gen spam filter appliances section are included as standard to maximize your defenses against malware, ransomware and phishing with minimum maintenance overheads.
Double anti-virus protection with phishing protection and malicious URL blocking is provided by two of the leading anti-virus platforms in the industry – Kaspersky Labs and Clam AV – and our easy-to-use service is supported by industry-leading customer and technical assistance. For more than 5,000 customers, SpamTitan has already proven to be the best spam filter appliance for business.
How Does SpamTitan’s Virtual Spam Filtering Appliance Block Spam Email?
Try SpamTitan´s Anti Spam Virtual Appliance for Free
If you have concerns about the volume of spam emails evading detection in your business, and you would like to better protect your network against phishing, malware and ransomware, you are invited to contact us and request a free trial of SpamTitan´s anti spam virtual appliance. Our Sales Technicians will be happy to guide you through the registration process and explain about the implementation process for starting your trial.
The trial of our anti spam virtual appliance gives you the opportunity to evaluate SpamTitan in your own environment with full customer and technical support throughout. By the end of the trial period, you should have found the optimum settings for each employee or department in your business so that, if you choose to continue with our service, no further configuration of our anti spam appliance will be necessary.
- Automatic updates reduce the maintenance overhead.
- Greylisting increases spam detection rates to 99.97%.
- Our web-based management portal simplifies policy application.
- Outbound mail scanning protects your business´s IP reputation.
- Try SpamTitan´s virtual anti spam appliance for free by calling us today.
Related Articles
Frequently Asked Questions (FAQs)
Why might an anti-spam appliance block the delivery of a potential lead?
An anti-spam appliance might block the delivery of a potential lead if, for example, an organization’s website uses contact forms for potential customers to complete and submit. Enquiries from online contact forms are usually delivered to sales teams by email; but, if the potential customer has poor English skills, uses spam-like salutations, or misspells words, an anti-spam appliance with a high confidence threshold may reject the email.
How could an outbound email include an infected attachment?
An outbound email could include an infected attachment in a number of scenarios. The easiest one to explain is if an employee has been working on a file on an infected personal device, and then brings the device into the workplace to download the file onto their work computer. If the infection is not quickly identified by anti-virus software, the file could be attached to an email and sent within minutes.
Is SpamTitan effective on Microsoft Exchange servers?
SpamTitan is effective on Microsoft Exchange servers and improves the spam detection rate while reducing the management overhead. SpamTitan automatically works with Exchange 2013, 2016, and 2019, and can be configured to work with Exchange 2010 servers that still rejects invalid recipients after they are specified rather than after the DATA command.
How does the spam detection rate of 99.97% compare with other appliances?
The spam detection rate of 99.97% compares very well with other anti-spam appliances. In March 2016, the independent antivirus software assessor – AV Comparatives – conducted a spam detection test on multiple anti-spam appliances. The average spam detection rate among the top ten performing appliances was 96.86%.
How does an anti-spam appliance work?
An anti-spam appliance works by using techniques such as content filtering, blacklisting, and pattern analysis to identify and block spam emails before they reach the intended recipients. Some also include additional features that greylist emails, scan attachments for viruses, and provide “time-of-click” protection to prevent users clicking on embedded URLs that passed the filtering process but have been subsequently weaponized.
Why are anti-spam appliances important?
Anti-spam appliances important because they help protect users from the negative effects of spam, including wasted time, increased network traffic, and potential security threats embedded within spam emails. In many cases, layering a specialist anti-spam appliance on top of a default email filter can be more straightforward that trying to configure the default email filter to block spam effectively.
Are anti-spam appliances effective in blocking all spam emails?
Anti-spam appliances are not effective in blocking all spam emails due to the constantly evolving nature of spam techniques. However, they significantly reduce the amount of spam that reaches users’ inboxes; and, as appliances’ machine learning capabilities improve, most anti-spam appliances will be capable of blocking all bar a few spam emails and other email borne threats.
Can anti-spam appliances mistakenly block legitimate emails?
Anti-spam appliances can mistakenly block legitimate emails from time to time. This may be because the filtering rules are too aggressive, or because a legitimate email contains language of a spam-like nature. Most appliances provide options to review and recover false positives, and it is also possible to create whitelists of trusted senders so their emails bypass the filtering process.
Can anti-spam policies be customized to meet specific needs?
Anti-spam policies can be customized to meet specific needs – either organization-wide, by department, or by individual user. A common example of customized policies is when more aggressive filtering policies are applied to departments with access to sensitive data (i.e., finance, legal, etc.), while more relaxed policies are applied to other departments (i.e., sales, marketing, etc.).