In this post we explain two of the most important strategies to adopt to block phishing and ransomware attacks.
Ensure Malicious Messages Do Not Reach Inboxes
Last year, Netwrix released a report based on a survey that showed 100% of government IT workers believed employees were the biggest threat to security. While those figures are the highest of many such surveys, the common theme throughout all of the research is employees are the most likely cause of a data breach.
One of the biggest areas of weakness is email-based attacks. Research conducted by the Friedrich Alexander University in Germany suggests half of users click links in emails from unknown senders. Those links often lead employees to phishing and malware-laced websites. With such high click rates, it is no surprise that so many IT workers believe employees are the weakest link in their security defenses.
Stopping employees from taking risky actions is difficult, so organizations must do all they can to ensure malicious emails are not delivered to inboxes. Only then, can IT workers be sure that employees will not click links or open dangerous email attachments.
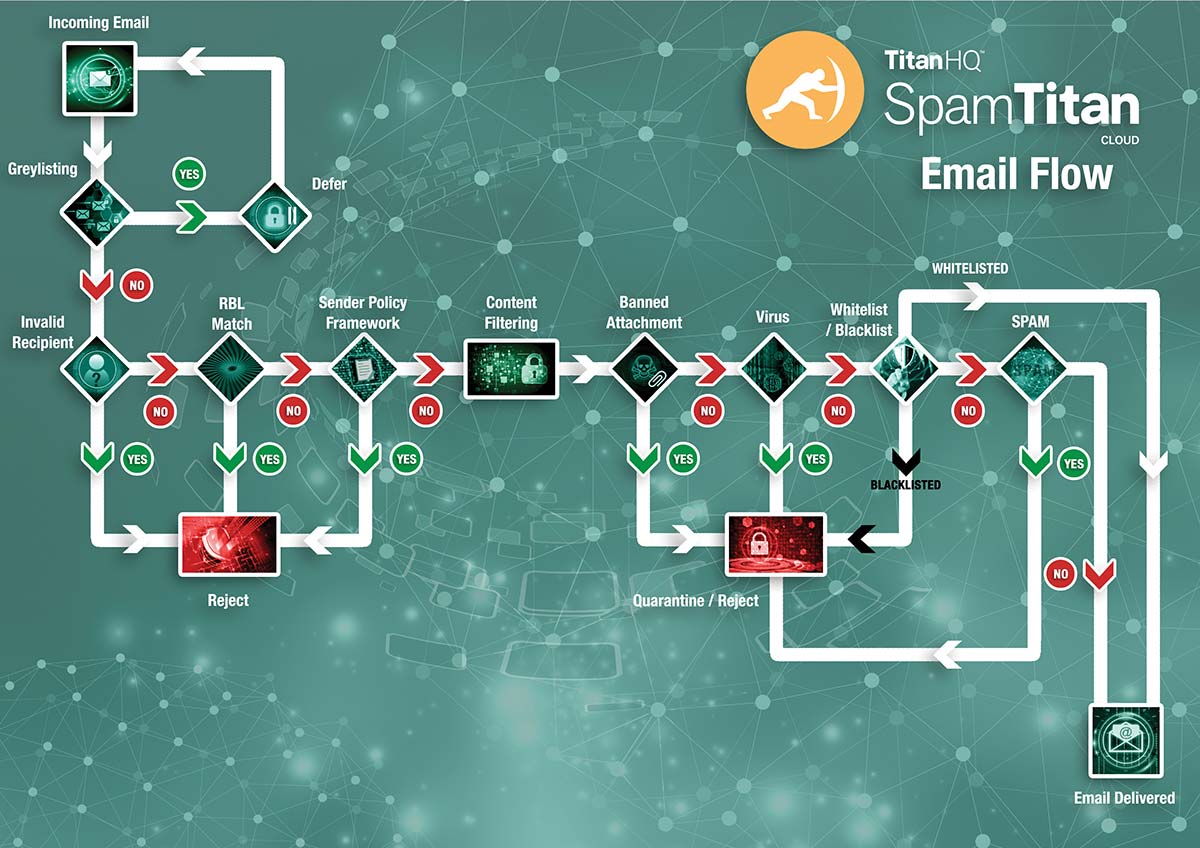
How Does SpamTitan Work?
There is No Silver Bullet That Will Block Phishing and Ransomware Threats 100% of the Time
No business can no survive without email and unfortunately, no spam filtering solution can block 100% of all spam emails, 100% of the time. At least not without also blocking many genuine messages. Organizations cannot rely on a spam filter to block phishing and ransomware threats. It is just one important layer of security. Several other layers are required.
Anti-virus and anti-malware solutions are essential for detecting malicious software, but these signature-based security controls are proving less and less effective as years go by. For instance, the solutions are not particularly good at detecting fileless malware.
Most businesses further reduce risk by implementing endpoint protection systems that can detect anomalies and unnatural behavior on endpoints, indicative of an intrusion, malware activity, or ransomware scanning for files and making changes.
However, AV software and endpoint detection systems only detect phishing and ransomware attacks when they are occurring. If you want to block phishing and ransomware attacks, the most effective solution is a human firewall.
IT departments can blame employees for being the weakest link when it comes to security, but if employees are not trained and shown how to recognize malicious emails, they will remain the biggest security threat to an organization.
The Human Firewall – The Best Defense Against Phishing, Malware, and Ransomware Emails
A firewall is the first line of defense, and anti spam software will help to keep inboxes free from malicious messages. The rear guard is made up of your employees. To ensure you have a strong defensive backline, you must provide security awareness training. Many employees do not know that they are taking big risks that could compromise the network. It is up to organizations to ensure that those risks are explained.
Most malware and ransomware attacks involve at least some user interaction: The clicking of a link, the opening of a malicious document, or the enabling of a macro. Employees must be told this is how malware is installed and how access to email accounts and networks is gained. By training the workforce to be more security aware, employees can be turned into a formidable last line of defense.
Security Awareness Training Should Be Continuous
While it was once possible to provide annual security training and be reasonably confident that employees would be able to recognize malicious emails, that is no longer the case. Email-based cyberattacks are now far more sophisticated, and cybercriminals are investing considerably more time in developing highly convincing campaigns. Cybercriminals’ tactics are constantly changing. Training programs must reflect that.
To develop a strong human firewall, training should be ongoing. An annual classroom-based training session should be accompanied by regular CBT training sessions, provided in bite-sized chunks. Cybersecurity should be kept fresh in the mind with monthly email bulletins, as well as ad hoc alerts about new threats.
Research conducted by several security awareness training companies shows, training is very effective. PhishMe, Wombat Security Technologies, and Knowbe4 all suggest that with regular training it is possible to reduce susceptibility to email-based attacks by up to 95%.
Test the Effectiveness of Security Awareness Training with Phishing Simulations
You can backup all your data to ensure you can recover files in the event of a disaster, but if your backups are never tested you can never be sure file recovery is possible.
Similarly, providing security awareness training to employees will not guarantee you have created a strong human firewall. Your firewall must be tested. By sending phishing simulations to your workforce you can find out just how effective your training has been. You can identify weak links – employees that have not grasped the concept of phishing and email security and those individuals can be scheduled additional training. Phishing simulation exercises also help to reinforce training. When a test is failed, it can be turned into a learning opportunity, which helps to improve knowledge retention.
Implement technological solutions to block phishing and ransomware attacks and train your employees and test them on all manner of email-based attacks. When the real deal arrives in an inbox they will be prepared and deal with it appropriately. Fail to block emails or provide high quality training, and your company is likely to have to deal with a costly, and potentially disastrous, email-based attack.