Phishing & Email Spam
Phishing and email spam is estimated to cost industry more than $1 billion each year, and cybercriminals are becoming more sophisticated in the campaigns they launch to try to extract confidential data or passwords from unsuspecting Internet users.
Part of the reason why phishing and email spam continue to work is the language used within the communication. The message to “Act Now” because an account seems to have been compromised, or because a colleague appears to need urgent support, often causes individuals to act before they think.
Even experienced security experts have been caught by phishing and email spam, and the advice provided to every Internet user is:
- If you are unsure of whether an email request is legitimate, try to verify it by contacting the sender independently of the information provided in the email.
- Never reveal confidential data or passwords requested in an email or on a web page you have arrived at after following a link in an email.
- Enable spam filters on your email, keep your anti-virus software up-to-date and enable two-step authentication on all your accounts whenever possible.
- Always use different passwords for different accounts, and change them frequently to avoid being a victim of key-logging malware downloads.
- Remember that phishing and email spam is not limited to email. Watch out for scams sent via social media channels.
Phishing in particular has become a popular attack vector for cybercriminals. Although phishing goes back to the early days of AOL, there has been a tenfold increase in phishing campaigns over the past decade reported to the Anti-Phishing Working Group (APWG).
Phishing is an extension of spam mail and can target small groups of people (spear phishing) or target executive-level management (whale phishing) in order to collect information or gain access to computer systems.
The best way to protect yourself from phishing and email spam is to follow the advice provided above and – most importantly – enable a reputable spam filter to block potentially unsafe emails from being delivered to your inbox.
by G Hunt |
January 26, 2021 |
Email Scams, Phishing & Email Spam
A new phishing campaign has been identified that abuses the Windows Finger command to download a malware variant called MineBridge.
The Finger command in Windows can be used by a local user to obtain a list of users on a remote machine or, alternatively, to obtain information about a specific remote user. The Finger utility originated in Linux and Unix operating systems but is also included in Windows. The utility allows commands to be executed to find out whether a particular user is logged on, although this is now rarely used.
There are also security concerns with the finger utility, and it has been abused in the past to find out basic information about users that can be targeted in social engineering attacks. Vulnerabilities in the finger protocol have also been exploited in the past by some malware variants.
Recently, security researchers discovered Finger can be used as a LOLBin to download malware from a remote server or to exfiltrate data without triggering alerts from security solutions. Finger is now being used in at least one phishing campaign to download malware.
MineBridge malware is a Windows backdoor written in C++ that has previously been used in attacks on South Korean companies. The malware was first identified in December 2020 by researchers at FireEye and in January 2020 several campaigns were identified distributing the malware via phishing emails with malicious Word attachments.
The latest campaign sees the attackers impersonate a recruitment company. The email is a recommendation of a candidate for consideration for a position at the targeted firm. The sender recommends even if there are no current openings, the CV should be checked, and the candidate considered. The email is well written and believeable.
As is common in phishing campaigns, if the document is opened a message will be displayed that tells the user the document has been created in an old version of Windows and to view the content the user needs to ‘enable editing’ and then ‘enable content’. Doing so will run the macro, which will fetch and download a Base64 encoded certificate using the Finger command. The certificate is a malware downloader that used DLL hijacking to sideload the MineBridge backdoor. Once installed, MineBridge will give the attacker control over an infected device and allow a range of malicious actions to be performed.
It is easiest to block attacks like this by installing an advanced spam filtering solution to block the malicious emails and prevent them from reaching inboxes. As an additional protection against this and other campaigns that abuse the Finger.exe utility in Windows, admins should consider disabling finger.exe if it is never used.
by G Hunt |
December 30, 2020 |
Email Scams, Phishing & Email Spam
Cybercriminals are leveraging interest in COVID-19 vaccination programs and are conducting a range of COVID-19 vaccine phishing scams with the goal of obtaining sensitive data such as login credentials or to distribute malware. Several government agencies in the United States have recently issued warnings to businesses and consumers about the scams including the Department of Health and Human Services’ Office of Inspector General and the Centers for Medicare and Medicaid Services, and law enforcement agencies such as the FBI.
COVID-19 vaccine scams can take many forms. Campaigns have already been detected that offer early access to COVID-19 vaccines. These scams require a payment to be made as a deposit or a fee to get to the top of the waiting list. Other scams offer the recipients a place on the waiting list if they apply and provide personal information.
COVID-19 vaccine phishing scams are being conducted via email; however, it is likely that fraudsters will advertise on websites, social media channels, or conduct scams over the telephone or via SMS messages and instant messaging platforms. While many of these scams target consumers, there is potential for businesses to be affected if employees access their personal emails at work or if the scam emails are sent to work email addresses.
Scam emails often include links to websites where information is harvested. These links may be hidden in email attachments to hide them from email security solutions. Office documents are also commonly used for delivering malware, via malicious macros.
The emails typically impersonate trusted entities or individuals. COVID-19 vaccine scam emails are likely to impersonate healthcare providers, health insurance companies, vaccine centers, and federal, state, or local public health authorities. During the pandemic, there have been many cases of fraudsters impersonating the U.S. Centers for Disease Control and Prevention (CDC) and the World Health Organization (WHO) in Covid-19-related phishing scams.
The U.S. Department of Justice recently announced that two domains have been seized that impersonated vaccine developers. The domains were virtual carbon copies of the legitimate websites of two biotechnology companies involved in vaccine development. The malicious content has been removed, but there are likely to be many more domains registered and used in COVID-19 vaccine phishing scams over the coming weeks.
Warnings have also been issued about the risk of ransomware attacks that take advantage of interest in COVID-19 vaccines and provide the attackers with the foothold in networks they need to conduct their attacks.
There are four important steps that businesses can take to reduce to risk of falling victim to these scams. Since email is extensively used, it is essential to have an effective spam filtering solution in place. Spam filters use blacklists of malicious email and IP addresses to block malicious emails, but since new IP addresses are constantly being used in these scams, it is important to choose a solution that incorporates machine learning. Machine learning helps to identify phishing threats from IP addresses that have not previously been used for malicious purposes and to identify and block zero-day phishing threats. Sandboxing for email is also important for identifying and blocking zero-day malware threats that have yet to have their signatures incorporated into the virus definition lists of antivirus engines.
While spam filters can identify and block emails that contain malicious links, a web filtering solution is also recommended. Web filters are used to control the websites that employees can access and prevent visits to malicious websites through general web browsing, redirects, and clicks on malicious links in emails. Web filters are constantly updated via threat intelligence feeds to provide protection against recently discovered malicious URLs.
Businesses should not neglect end user training and should regularly provide refresher training to employees to help them identify phishing threats and malicious emails. Phishing simulation exercises are also beneficial for evaluating the effectiveness of security awareness training.
Multi-factor authentication should also be applied as a last line of defense. In the event of credentials being compromised, multi-factor authentication will help to ensure that stolen credentials cannot be used to remotely access accounts.
With these measures implemented, businesses will be well protected from malware, COVID-19 vaccine phishing scams, and other phishing threats.
For further information on spam filtering, web filtering, and protecting your business from malware and phishing attacks, give the TitanHQ team a call today.
by G Hunt |
December 28, 2020 |
Network Security, Phishing & Email Spam
Recently, a new technique has been identified that is being used by hackers to conduct cross-site scripting attacks from within PDF files.
PDF files have long been used by hackers for phishing attacks and malware delivery. Oftentimes, emails are sent with PDF file attachments that contain hyperlinks to malicious websites. By adding these links into the files rather than the body of the email message, it is harder for security solutions to identify those malicious links.
The latest attack method also uses PDF files, but instead of tricking employees into revealing their login credentials or visiting a malicious website where malware is downloaded, the attackers attempt to obtain sensitive information contained in PDF files.
The technique is similar to those used to by hackers in web application attacks. Cross-site scripting attacks – or XXS attacks for short – typically involve injecting malicious scripts into trusted websites and applications. When a user visits a website or a hacked application, the script executes. The scripts give the attackers access to user information such as cookies, session tokens, and sensitive data saved in browsers, such as passwords. Since the website or application is trusted, the web browser will not recognize the script as malicious. These attacks are possible in websites and web applications where user input is used to generate output without properly validating or encoding it.
The same technique has been shown to also work within PDF files and is used to inject code and capture data. This is achieved by taking advantage of escape characters such as parentheses, which are commonly used to accept user input. If the input is not validated correctly, hackers can inject malicious URLs or JavaScript code into the PDF files. Even injecting a malicious URL can be enough to capture data in the document and exfiltrate it to the attacker-controlled website, as was demonstrated at the Black Hat online conference this month.
What sort of data could be captured in such an attack? A substantial amount of sensitive data is contained in PDF files. PDF files are used extensively for reports, statements, logs, e-tickets, receipts, boarding passes, and much more. PDF files may contain passport numbers, driver’s license numbers, bank account information, and a range of other sensitive data. The presenters at the conference explained they found some of the largest libraries of PDF files worldwide were sensitive to XXS attacks.
In the most part, the vulnerabilities in PDF files that allow XXS attacks are not due to the PDF files themselves, but improper coding. If PDF libraries fail to properly parse code of escape characters and allow unprotected formats, they will be vulnerable. Fortunately, Adobe released an update on December 9 which prevents this type of security vulnerability from being exploited, although companies that create PDF files must update their software and apply the update to be protected.
This is just one way that malicious attachments can be used to obtain sensitive information. As previously mentioned, malicious macros are commonly added to office documents, executable files are added as attachments to emails and masquerade as legitimate files, and malicious code can be injected into a range of different file types.
One of the best ways to protect against attacks via email using malicious attachments is to use an advanced email security solution that can detect not just known malware but also never-before-seen malicious code. This is an area where SpamTitan Email Security excels.
SpamTitan incorporates dual anti-virus engines (Bitdefender/ClamAV) to catch known malware threats and email sandboxing to identify malicious code that has been added to email attachments. Files are subjected to in-depth analysis in the security of the sandbox and are checked for any malicious actions.
To find out more about protecting your organization from malicious emails and malware, give the TitanHQ team a call.
by G Hunt |
November 26, 2020 |
Phishing & Email Spam, Spam Advice, Spam News
Banking Trojans have long posed a threat to businesses, but one in particular has stood head and shoulders above the rest in 2020: The Emotet Trojan.
Emotet: The Biggest Malware Threat in 2020
The Emotet Trojan first appeared in 2014 and was initially a banking Trojan, which was used to steal sensitive data such as bank account information from browsers when the user logs into their bank account. The Emotet Trojan has since been developed and it has now evolved into a much bigger threat.
Emotet is now far more effective at spreading to other devices, using a worm like element to infect other devices on the network as well as hijacking the user’s email account and using it to send copies of itself to victims’ contacts. Infected devices are added to the Emotet botnet, and have been used in attacks on other organizations. The operators of Emotet have now joined forces with other cybercriminal operations and are using their malware to deliver other Trojans such as TrickBot and QakBot, which in turn are used to deliver ransomware.
Data from HP Inc. revealed Emotet infections increased by 1,200% from Q2 to Q3, showing the extent to which activity has increased recently. Data from Check point show Emotet is the biggest malware threat, accounting for 12% of all infections in October 2020. TrickBot, which is delivered by Emotet, is the second biggest threat, accounting for 4% of infections.
Emotet and TrickBot are Driving the Increase in Ransomware Infections
The Emotet and TrickBot Trojans are driving the increase in ransomware infections globally, especially attacks on healthcare organizations. The healthcare industry in the United States is being targeted by ransomware gangs due to the increased chance of the ransom being paid. In many cases, the recent ransomware attacks have been made possible due to previous Emotet an TrickBot infections.
Unfortunately, due to the efficient way that Emotet spreads, removing the malware can be problematic. It is probable that more than one device has been infected, and when the Trojan is removed from one device, it is often reinfected by other infected devices on the network.
Emotet is primarily spread via phishing emails, most commonly using malicious macros in Word documents and Excel spreadsheets, although JavaScript attachments are also known to be used. The lures used in the phishing emails are highly varied, often using topical lures linked to recent news events, COVID-19, and holiday season lures in the run up to Halloween, Black Friday, and Cyber Monday.
The best way of preventing attacks is stopping the Emotet emails from reaching inboxes and making sure that employees are trained how to recognize phishing emails.
How SpamTitan Can Protect Your Organization
SpamTitan use a wide range of different techniques to identify phishing emails that are used to deliver malware such as Emotet. These measures provide layered protection, so should one check fail to identify the threat, several others are in place to provide protection.
SpamTitan uses dual antivirus engines to identify previously seen malware variants and email sandboxing to identify new (zero day) malware threats. Suspicious email attachments are sent to the sandbox where they are subjected to in depth analysis to identify malicious actions such as command and control center callbacks.
Users can set controls to quarantine or reject messages with certain types of email attachments, and while blocking Word and Excel documents and spreadsheets is not practical for most businesses, setting rules to quarantine these files for manual review if they have macros is certainly wise, as is blocking JavaScript files and other file types commonly used to install malware.
SpamTitan uses Sender Policy Framework (SPF) and DMARC to block spoofing and email impersonation attacks, which are used to convince employees to open attachments and click malicious links. SpamTitan also includes outbound scanning, which detects devices that have potentially been infected and prevents messages from spreading Emotet internally and to business contacts.
There are many cybersecurity solutions that can provide protection against malware, but finding one that is easy to use, effective, and reasonably priced can be a challenge.
SpamTitan ticks all of those boxes. It is the most and best ranked email security solution on Capterra, GetApp and Software Advice, has achieved a rating of 4.9 out of 5 on Google reviews, and is listed in the top three in the email security gateway, MSP email security, and email security for Office 365 categories.
If you want to protect your organization from Emotet and other malware and phishing attacks, give the TitanHQ team a call to find out more about SpamTitan Email Security.
by G Hunt |
August 14, 2020 |
Email Scams, Phishing & Email Spam, Spam News
Several SBA loan phishing scams identified in recent weeks that impersonate the U.S. Small Business Administration in order to obtain personally identifiable information and login credentials for fraudulent purposes.
Due to the hardships suffered by businesses due to the COVID-19 pandemic, the SBA’s Office of Disaster Assistance is offering loans and grants to small businesses to help them weather the storm.
Hundreds of millions of dollars have been made available by the U.S. government under the Coronavirus Aid, Relief, and Economic Security Act (CARES Act) to help struggling individuals and companies during the pandemic. Cybercriminals have been quick to develop campaigns to fraudulently obtain those funds, raid bank accounts, steal sensitive information, and distribute malware and ransomware.
Several phishing campaigns have been launched since April 2020 targeting businesses that are considering or have already applied for loans under the SBA’s Economic Injury Disaster Loan Program.
Phishing emails have been sent encouraging small businesses to apply for a loan. One such campaign confirms that the business is eligible for a loan and the loan has been pre-approved. The purpose of the scam is to obtain business information that allows the scammers to apply for a loan on behalf of the business and pocket the funds.
Another scam impersonates the SBA and claims an application for a loan is complete and payment will be made once supporting documents have been received. The emails include an attached form that must be completed and uploaded to the SBA website. The email attachment appears to be a .img file but has a hidden double extension and is actually a .exe executable. Double-clicking and running the file will see GuLoader malware installed, which is a downloader that can deliver a range of different malicious payloads.
The same email address used for that campaign was used in a different attack that included a PDF form that requested bank account information and other sensitive data, which needed to be completed and uploaded to a spoofed SBA website.
In the past few days, yet another SBA loan phishing scam has come to light. Phishing emails were sent to Federal Executive Branch, and state, local, tribal, and territorial government agencies. The phishing scam relates to an SBA application for a loan with the subject line “SBA Application – Review and Proceed.” The emails links to a cleverly spoofed SBA web page that indistinguishable from the genuine login page apart from the URL that attempts to steal credentials. The scam prompted the DHS’ Cybersecurity and Infrastructure Security Agency (CISA) to issue an emergency alert warning of the scam.
These SBA loan phishing scams use a variety of lures and have multiple aims, but they can be avoided by following good cybersecurity best practices.
First and foremost, you should have an advanced spam filtering solution in place such as SpamTitan. SpamTitan checks email headers and message content for signs of spam, phishing, and scams and uses DMARC and sender policy framework (SPF) to identify and block email impersonation attacks.
Dual antivirus engines detect 100% of known malware and sandboxing is used to subject attachments to deep analysis to identify malicious code and malware that has not been seen before. Machine learning technology is also used to identify new phishing scams, along with multiple threat intelligence feeds to identify known phishing scams.
Prior to opening any downloaded document or file it should be scanned using antivirus software that has up-to-date virus definitions. Check the properties of files to make sure they are what they claim to be and do not have a double extension.
Care should be taken when opening any email or email attachment, even emails that are expected. Steps should be taken to verify the legitimacy of any request received via email, especially one that requires the provision of personally identifiable information or requests for bank account and other highly sensitive information.
Emails and websites may look legitimate and have SBA logos, but that does not guarantee they are genuine. Always carefully check the sender of the email – Genuine SBA accounts end with sba.gov. The display name can easily be spoofed so click reply and carefully check the email address is correct. Care should be taken when visiting any website linked in an email. Check the full URL of any website to make sure it is a legitimate domain.
CISA also recommends monitoring users’ web browsing habits and restricting access to potentially malicious websites. The easiest way to do this is by using a web filtering solution such as WebTitan. WebTitan allows businesses to monitor Internet activity in real time, send automatic alerts, block downloads of certain file types, and carefully control the types of websites that can be accessed by employees.
For more information on spam filtering and web filtering solutions to protect your business from phishing and other cyberattacks, give the SpamTitan team a call today.
by G Hunt |
July 31, 2020 |
Network Security, Phishing & Email Spam
Over the past few months, cyberattacks involving Netwalker ransomware have been steadily increasing and Netwalker has now become one of the biggest ransomware threats of 2020.
Netwalker ransomware is the new name for a ransomware variant called Mailto, which first appeared a year ago in August 2019. The threat actors behind the ransomware rebranded their malware as Netwalker in late 2019 and in 2020 started advertising for affiliates to distribute the ransomware under the ransomware-as-a-service model. In contrast to many RaaS offerings, the threat group is being particularly choosy about who they recruit to distribute the ransomware and has been attempting to build a select group of affiliates with the ability to conduct network attacks on enterprises that have the means to pay large ransoms and the data to warrant such large payments if attacked.
Netwalker ransomware was used in an attack in February on Toll Group, an Australian logistics and transportation company, which caused widespread disruption although the firm claims not to have paid the ransom. Like several other ransomware gangs, the Netwalker gang took advantage of the COVID-19 pandemic and was using COVID-19 lures in phishing emails to spread the ransomware payload via a malicious email attachment, opting for a Visual Basic Scripting (.vbs) loader attachments.
Then followed attacks on Michigan State University and Columbia College of Chicago, with the frequency of attacks increasing in June. The University of California San Francisco, which was conducting research into COVID-19, was attacked and had little choice other than to pay the $1.14 million ransom demand to regain access to essential research data that was encrypted in the attack. More recently Lorien Health Services, a Maryland operator of assisted living facilities, also had files encrypted by the Netwalker gang.
The recent attacks have seen the attack vector change, suggesting the attacks have been the work of affiliates and the recruitment campaign has worked. Recent attacks have seen a range of techniques used in attacks, including brute force attacks on RDP servers, exploitation of vulnerabilities in unpatched VPN systems such as Pulse Secure VPNs that have not had the patch applied to correct the CVE-2019-11510 vulnerability. Attacks have also been performed exploiting user interface components of web apps, such as the Telerik UI vulnerability CVE-2019-18935, in addition to vulnerabilities in Oracle WebLogic and Apache Tomcat servers.
With the ransoms paid so far, the group is now far better funded and appears to have skilled affiliates working at distributing the ransomware. Netwalker has now become one of the biggest ransomware threats and has joined the ranks of Ryuk and Sodinokibi. Like those threat groups, data is stolen prior to file encryption and threats are issued to publish or sell the data if the ransom is not paid.
The increase in activity and skill of the group at gaining access to enterprise networks prompted the FBI to issue a flash alert warning of the risk of attack in late July. The group appears to be targeting government organizations, educational institutions, healthcare providers and entities involved in COVID-19 research, and the attacks are showing no sign of slowing, in fact they are more than likely to increase.
Defending against the attacks requires a defense in depth approach and adoption of good cyber hygiene. An advanced spam filtering solution should be used to block email attacks, end users should be taught how to recognize malicious emails and shown what to do if a suspicious email is received. Vulnerabilities in software are being exploited so prompt patching is essential. All devices should be running the latest software versions.
Antivirus and anti-malware software should be used on all devices and kept up to date, and policies requiring strong passwords to be implemented should be enforced to prevent brute force tactics from succeeding. Patched VPNs should be used for remote access, two-factor authentication should be implemented, web filters used for secure browsing of the internet, and backups should be performed regularly. Backups should be stored on a non-networked device that is not accessible over the internet to ensure they too are not encrypted in an attack.
by G Hunt |
July 27, 2020 |
Phishing & Email Spam
Football is big business and large quantities of money are often transferred electronically between clubs to bring in new players. If scammers were to insert themselves into the communications between clubs, huge payments could easily be diverted. In 2018, the Italian football club Lazio was targeted with a phishing scam that resulted in a payment of €2 million being sent to an account under the control of scammers. The money was never recovered.
Now it appears that the sports industry is being targeted again. Recently, a similar scam was conducted on a Premier League football club in England. The hackers gained access to the email account of the managing director of the club through a phishing campaign after directing the MD to a domain where Office credentials were harvested. Those credentials were then used to access the MD’s email account, and the scammers inserted themselves into and email conversation with another club looking to purchase a player. Fortunately, the scam was detected by the bank and a £1 million fraudulent payment was blocked.
This type of scam starts with a phishing email but is referred to as a Business Email Compromise (BEC) scam. BEC scams are commonplace and often successful. They range from simple scams to complicated multi-email communications between two parties, whether one party believes they are communicating with the genuine email account holder when they are actually communicating with the scammer. When the time comes to make payment, the scammer supplies their own account credentials. All too often, these scams are not detected until after payment is made.
That is far from the only cyberattack on the sports industry in recent weeks and months. There have been several attempted cyberattacks which prompted to the UK’s National Cyber Security Center (NCSC) to issue a warning advising the UK sports sector to be on high alert.
Prior to lockdown, a football club in the UK was hit with a ransomware attack that encrypted essential systems, including the computer systems that controlled the turnstiles, preventing them from working. A game nearly had to be abandoned due to the attack. The ransomware attack is suspected to have also started with a phishing email.
The recent attacks are not limited to football clubs. NCSC data show that 70% of sports institutions in the United Kingdom have suffered a cyberattack in the past 12 months.
NCSC figures show approximately 30% of incidents resulted in financial losses, with the average loss being £10,000, although one organization lost £4 million in a scam. 40% of the attacks involved the use of malware, which is often delivered via spam email. A quarter of attacks involved ransomware.
While malware and ransomware attacks are costly and disruptive, the biggest cause of losses is BEC attacks. Figures from the FBI show these scams accounted for around half of all losses to cybercrime in 2019. $1.77 billion was lost to BEC attacks in 2019, with an average loss of $75,000 (£63,333). The true figure is likely to be even higher, as not all BEC attacks are reported. The FBI anticipates even greater losses this year.
While there are many different attack methods, email remains the most common vector used in cyberattacks on businesses. It is therefore essential to implement a robust email security solution that can block malicious emails and prevent them from being delivered to inboxes.
TitanHQ has developed a powerful, advanced email security solution that can help businesses improve their email security defenses and block phishing, spear phishing, BEC, malware, and ransomware attacks. SpamTitan incorporates multiple threat intelligence feeds, machine learning systems to identify phishing attempts, dual anti-virus engines, and a sandbox to subject suspicious email attachments to in-depth analysis. SpamTitan also incorporates SPF and DMARC to identify and block email impersonation attacks.
If you are concerned about email security and want to improve your defenses against email threats, give the TitanHQ team a call to find out more about SpamTitan and other security solutions that can help you defend your organization from cyberattacks.
Our customer service team will be happy to discuss your options and help set you up for a free trial so you can see for yourself the difference SpamTitan makes to email security.
by G Hunt |
May 27, 2020 |
Phishing & Email Spam
A U.S. Supreme Court phishing campaign has been detected that uses a fake subpoena to appear in court as a lure to obtain Office 365 credentials. The emails are personalized and are addressed to the victim and claim to be a writ issued by the Supreme Court demanding the recipient attend a hearing. This is a targeted campaign rather than a spray and pray attack that attempts to obtain the credentials of high value targets such as C-Suite members.
The emails include a link that the recipient is required to click to view the subpoena. Clicking the link in the email directs the user to a malicious website where they are required to enter their Office 365 credentials to view the subpoena.
The domain used is brand new and, as such, it is not recognized as malicious by many security solutions, including the default anti-phishing measures of Office 365. The scammers have also used multiple redirects to hide the destination URL in another attempt to thwart anti-phishing defenses.
Prior to the user being directed to the phishing page, they are presented with a CAPTCHA page. CAPTCHA is used to prevent web visits by bots, but in this case, it may be used to add legitimacy to the phish to make the request appear genuine. The CAPTCHA page is real, and the user must correctly select the images in order to proceed. The page also includes the name of the user, further adding legitimacy to the scam. The CAPTCHA may also be a further attempt to make it difficult for the destination URL to be analyzed by security solutions.
This phishing campaign is realistic and uses urgency to get the user to take action quickly, rather than stopping to think about the request. There are signs that this is a scam, such as the domain name which clearly has nothing to do with the U.S. Supreme Court, and a few grammatical and spelling mistakes which would not be expected of any Supreme Court request.
However, the sender name in the email was spoofed to make it appear to have been sent by the “Supreme Court”, the request is certain to scare some recipients into clicking the link, and the landing page is sufficiently realistic to fool busy employees into disclosing their login credentials.
Exchange Online protection (EOP), which is provided by Microsoft free of charge with all Office 365 accounts, often fails to spot these zero-day attacks.
To improve protection against new phishing campaigns, an anti-spam solution is required that incorporates predictive techniques, threat intelligence feeds, and machine learning algorithms. SpamTitan incorporates these and several other layers of protection to identify zero-day phishing, malware, and ransomware campaigns and email impersonation attacks.
SpamTitan can be layered on top of Microsoft’s Exchange Online Protection to serve as an additional layer to your email security defenses to ensure that more malicious emails are blocked and never reach end users inboxes.
by G Hunt |
April 27, 2020 |
Email Scams, Phishing & Email Spam
Higher education institutions in the United States are being targeted in a phishing campaign that distributes a remote access trojan called Hupigon, a RAT that was first identified in 2010.
The Hupigon RAT has previously been used by advanced persistent threat groups (APT) from China, although this campaign is not believed to have been conducted by APT groups, instead the Hupigon RAT has been repurposed by cybercriminals. While several industries have been targeted in the campaign, almost half of attacks have been on colleges and universities.
The Hupigon RAT allows the operators to download other malware variants, steal passwords, and gain access to the microphone and webcam. Infection could see the attackers take full control of an infected device.
The campaign uses online dating lures to get users to install the Trojan. The emails show two dating profiles of supposed users of the platform, and the recipient is asked to select the one they find the most attractive. When the user makes their choice, they are directed to a website where an executable file is downloaded, which installs the Hupigon RAT.
The choice of lure for the campaign is no doubt influenced by the huge rise in popularity of dating apps during the COVID-19 pandemic. While there are not many actual dates taking place due to lockdown and social distancing measures now in place around the globe, the lockdowns have seen many people with a lot of time on their hands. That, coupled with social isolation for many singles, has actually led to an uptick in the use of online dating apps, with many users of the apps turning to Zoom and FaceTime to have virtual dates. Several popular dating apps have reported an increase in use during the COVID-19 pandemic. For example, Tinder reports use has increased, with the platform having its busiest ever day, with more than 3 billion profiles swiped in a single day.
As we have already seen with COVID-19 lures in phishing attacks, which account for the majority of lures during the pandemic, when there is interest in a particular event or news story, cybercriminals will take advantage. With the popularity of dating apps soaring, we can expect to see an increase in the number of online dating -themed lures.
The advice for higher education institutions and businesses is to ensure that an advanced spam filtering solution is in place to block the malicious messages and ensure they do not reach end users’ inboxes. It is also important to ensure that security awareness training continues to be provided to staff, students, and remote employees to teach them how to recognize the signs of phishing and other email threats.
TitanHQ can help with the former. If you want to better protect staff, students, and employees and keep inboxes free of threats, give the TitanHQ team a call today. After signing up, you can be protecting your inboxes in a matter of minutes.
by G Hunt |
April 22, 2020 |
Email Scams, Phishing & Email Spam
Healthcare providers are being targeted by cybercriminals using COVID-19-themed phishing emails, with the campaigns showing no sign of letting up. The volume of attacks has prompted the U.S. Federal Bureau of Investigation (FBI) to issue a further warning to healthcare providers urging them to take steps to protect their networks and block the attacks.
The first major COVID-19-themed phishing attacks targeting healthcare providers started to be detected by around March 18, 2020. The attacks have grown over the following weeks and the lures have diversified.
Campaigns have been conducted targeting at-home healthcare employees who are providing telehealth services to patients, and there has been an increase in business email compromise scams. The latter see vendors impersonated and requests sent for early or out-of-band payments due to difficulties that are being experienced due to COVID-19.
The phishing attacks are being conducted to obtain login credentials and to spread malware, both of which are used to gain a foothold in healthcare networks to allow follow-on system exploitation, persistence, and the exfiltration of sensitive data.
The malware being distributed in these campaigns is highly varied and includes information stealers such as Lokibot, backdoors, and Trojans such as Trickbot. Microsoft has recently reported that Trickbot accounts for the majority of COVID-19 phishing emails targeting Office 365 users, with a campaign last week involving hundreds of different, unique macro-laced documents. In addition to being a dangerous malware variant in its own right, Trickbot also downloads other malicious payloads, including RYUK ransomware.
A diverse range of malware is delivered by a similarly diverse range of email attachments and malicious scripts. Microsoft Word documents containing malicious macros are commonly used, as are 7-zip compressed files, Microsoft executables, and JavaScript and Visual Basic scripts. The emails are being sent from a combination of domestic and international IP addresses.
While the number of COVID-19-themed phishing emails has been increasing, the overall volume of phishing emails has not increased by a major amount. What is happening is threat actors are changing their lures and are now using COVID-19 lures as they are more likely to be opened.
The campaigns can be highly convincing. The lures and requests are plausible, many of the emails are well written, and authorities on COVID-19 such as the Centers for Disease Control and Prevention, the HHS’ Centers for Medicare and Medicaid Services, and the World Health Organization have been spoofed. Oftentimes the emails are sent from a known individual and trusted contact, which makes it more likely that the email attachment will be opened.
The advice offered by the FBI is to follow cybersecurity best practices such as never opening unsolicited email attachments, regardless of who appears to have sent the email. Ensuring software is kept up to date and patches are applied promptly is also important, as is turning off automatic email attachment downloads. The FBI has also recommended filtering out certain types of attachments through email security software, something that is easy to do with SpamTitan.
The FBI has stressed the importance of not opening email attachments, even if antivirus software says that the file is clean. As the Trickbot campaign shows, new variants of malicious documents and scripts are being created at an incredible rate, and signature-based detection methods cannot keep up. This is another area where SpamTitan can help. In addition to using dual antivirus engines to identify known malware variants faster, SpamTitan includes sandboxing to identify and block zero-day malware threats that have yet to have their signatures added to antivirus software virus definitions lists.
Training is important to teach healthcare employees cybersecurity best practices to help them identify phishing emails, but it is also important to ensure that your technical controls are capable of blocking these threats.
by G Hunt |
March 24, 2020 |
Phishing & Email Spam, Spam Software
In this post, we explore email security and home working and offer advice to help businesses ensure their workers, devices, and networks are protected.
The 2019 Novel Coronavirus pandemic has forced many workers to self-isolate at home and an increasing number of employees want to work from home to reduce the risk of contracting COVID-19. Businesses are under pressure to allow their workers to stay at home and use either company-issued or personal devices to access their networks and work remotely.
Cybercriminals are constantly changing their tactics, techniques, and procedures and they have jumped at the opportunity provided by the Novel Coronavirus. People are scared and rightly so. COVID-19 has a high mortality rate and the virus is spreading like wildfire. People want information about cases in their local area, advice on how to protect themselves, and information about possible cures. Cybercriminals have obliged and are conducting phishing campaigns that claim to offer all that information. Many campaigns have now been detected from many different threat groups that attempt to obtain login credentials and spread malware. Since early January when the first major campaigns were detected, the volume of coronavirus and COVID-19 emails has increased significantly.
Campaigns are being conducted impersonating authorities on the Novel Coronavirus and COVID-19, such as the World Health Organization (WHO), the U.S. Centers for Disease Control and Prevention (CDC), the U.S. Department of Health and Human Services, and other government agencies. COVID-19-themed emails are being sent to remote workers that spoof HR departments warning about cases that have been detected within the organization. Health insurers are being spoofed in campaigns that include invoices for coverage for COVID-19.
Since January, more than 16,000 Coronavirus and COVID-19-themed domains have been registered which are being used to host phishing kits and distribute malware. Researchers at CheckPoint Software report that those domains are 50% more likely to be malicious than other domains registered in the same period.
Email security and home working will naturally be a major concern for IT teams given the sheer number of home workers due to the Coronavirus pandemic and the volume of attacks that are now being conducted targeting home workers. With so many devices now connecting to networks remotely, if cybercriminals do obtain credentials, it will be much harder for IT teams to identify threat actors connecting remotely. Fortunately, there are steps that can be taken to improve email security and home working need not majorly increase risk.
You should make sure that your employees can only connect to your network and cloud-based services through a VPN. Enterprise VPNs can be configured to force all traffic through the VPN to reduce the potential for error. Make sure that the VPN is configured to start automatically when the device is powered up.
It is crucial that all remote workers are protected by a robust and effective email security solution. It is not possible to stop cybercriminals targeting remote workers, but it is possible to stop phishing and malware threats from reaching inboxes.
To protect your employees against phishing attacks and malware, an advanced email security solution is essential. If you use Office 365 for email, do not rely on Office 365 email security. You will need greater protection than Exchange Online Protection provides to protect against phishing, spear phishing, and zero-day threats.
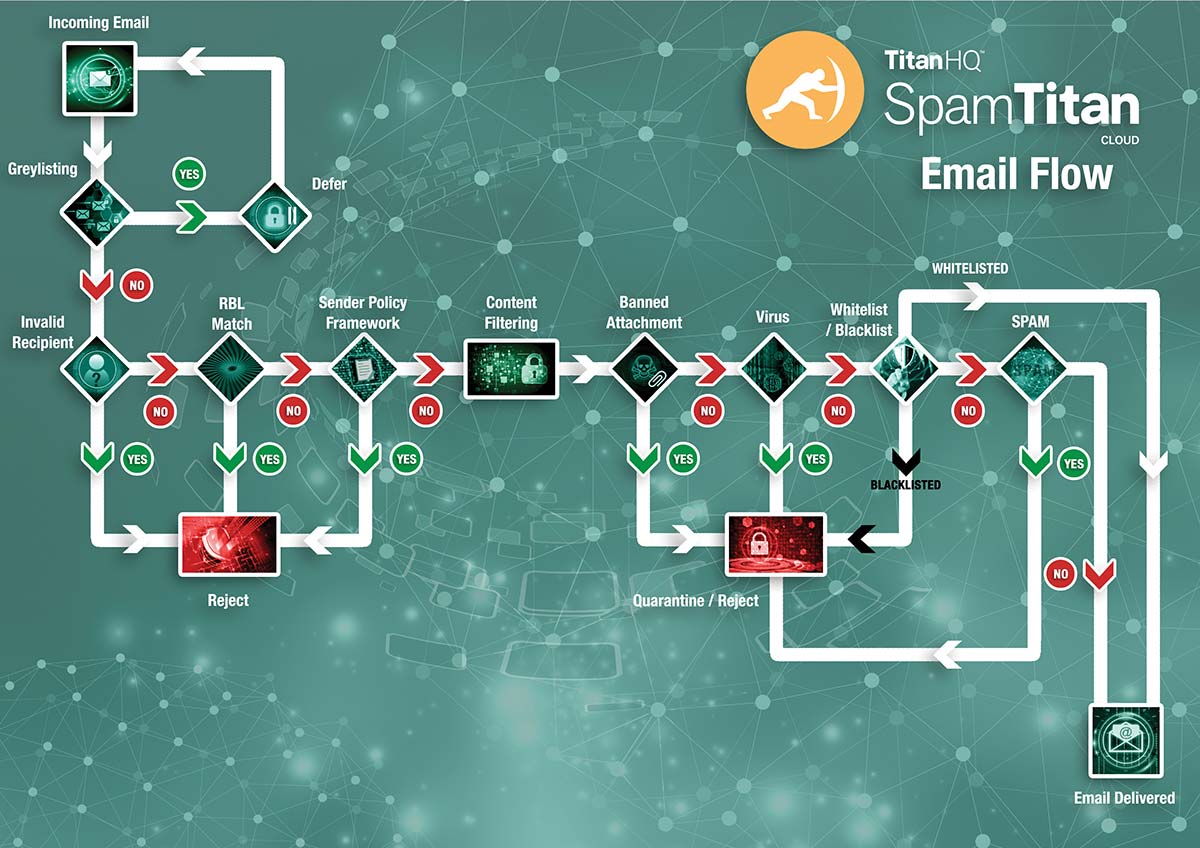
SpamTitan has multiple detection mechanisms to identify and block the full range of email threats. SpamTitan incorporates SPF and DMARC to provide protection against email impersonation attacks, machine learning algorithms and predictive technology to protect against zero-day attacks, advanced phishing protection from whaling and spear phishing attacks by scanning inbound email in real-time, dual antivirus engines to block malware threats, and email sandboxing for in-depth analysis of suspicious attachments. SpamTitan also includes 6 specialist RBLs, supports whitelisting, blacklisting, and greylisting, and incorporates multiple threat intelligence feeds.
There is an increased risk of insider threats with remote workers. To provide protection and prevent accidental policy violations, SpamTitan incorporates a data loss prevention filter to stop credit card numbers, Social Security numbers, and other data types from being sent via email.
No email security solution will be able to block 100% of email threats, 100% of the time. It is therefore important to provide regular cybersecurity training to employees to make them aware of phishing threats, train them how to identify a phishing email or social engineering scam, and to condition remote employees how to respond should a threat be received. Phishing simulation exercises are also useful to find out which employees require additional training and to identify possible gaps in training programs. IT security basic training refreshers should also be provided to ensure employees know what can and cannot be done with work devices.
Multifactor authentication must be implemented on all applications and email accounts to provide protection in the event of an account compromise. If credentials are stolen and used from a previously unknown location or an unfamiliar device, a second authentication factor must be provided before access is granted. You should also disable macros on all user devices unless a specific user needs to use macros for work.
You can arrange a demonstration to see SpamTitan in action and you can also sign up for a free trial to put SpamTitan to the test in your own environment.
by G Hunt |
March 12, 2020 |
Email Scams, Phishing & Email Spam, Spam Advice
Several new COVID-19 phishing email campaigns have been detected over the past few days that are exploiting fear about the novel coronavirus pandemic to deliver computer viruses and steal sensitive information.
People are naturally worried about getting infected with the real virus especially with the high fatality rate, so emails related to COVID-19 are likely to be opened.
Some of the phishing emails that have been intercepted are easy to identify as malicious. They are poorly written with spelling mistakes and grammatical errors, but some campaigns have been expertly crafted and are highly convincing and are likely to catch out many people.
The first COVID-19 phishing campaigns were detected in January and the number has steadily grown over the past few weeks. Many different threat groups are now using COVID-19 phishing lures to fool the unwary into disclosing credentials, visiting malicious links, or downloading malware.
The World Health Organization (WHO) has issued a warning after several phishing campaigns were detected that impersonated WHO. The emails claimed to provide essential information about cases in the local area along with advice on how to avoid infection. One of the most recently detected campaigns claimed to provide “Coronavirus Updates” with the emails containing a ZIP file attachment that appeared to be a PDF file – MYHEALTH.PDF. However, the file was actually an executable file – MYHEALTH.exe. If the file was opened, it triggered the download of GULoader, which in turn downloads Formbook malware from Google Drive. Another similar campaign included a Word attachment that downloaded the TrickBot Trojan, which is being used to deliver Ryuk ransomware as a secondary payload.
The Centers for Disease Control and prevention is also being impersonated. One campaign claims the novel coronavirus had become an airborne threat and warns of new cases in the local area. The emails appear to have been sent from a legitimate CDC email account – CDC-Covid19[@]cdc.gov. The emails include an attachment titled “Safety Precautions” which appears to be an Excel spreadsheet, but it actually a .exe executable file. Double clicking on the file attachment triggers the download of a banking Trojan.
Email and text-based phishing campaigns are targeting UK taxpayers and impersonate HM Revenue and Customs (HMRC). The emails include a legitimate HMRC logo and advise the recipients about a new COVID-19 tax refund program. According the emails, the refund program was set up in cooperation with National Insurance and National Health Services and allows taxpayers to claim back tax to help deal with the coronavirus pandemic. In order to receive the refund, the user is told they must supply their name, address, mother’s maiden name and their bank card number.
In the past few days, a web-based malware distribution campaign has been identified. Several websites are now displaying world maps and dashboards that allow people to track the spread of the virus and find out about the location of new cases. People are naturally concerned about cases in their local area, and the website maps are attracting a lot of visitors.
Shai Alfasi, a security researcher at Reason Labs, discovered several websites using fake versions of maps and dashboards. The websites prompt users to download an application that allows them to track infections in real-time. The application is an executable file that delivers the AZORult information stealer.
With COVID-19 infections increasing and showing no sign of slowing, COVID-19 phishing campaigns are likely to continue. Organizations should raise awareness of the threat of COVID-19 phishing attacks with their employees and ensure appropriate technical solutions are implemented to block web and email-based attacks. TitanHQ can help with the latter and can provide advanced email and web security solutions to block these attacks. If you have not yet implemented a web filter or email security solution to protect your Office 365 accounts, now is a good time to start. Contact TitanHQ today for further information.
by G Hunt |
February 17, 2020 |
Phishing & Email Spam, Spam News
Just a few days after new figures from the FBI confirmed business email compromise scams were the biggest cause of losses to cybercrime, news broke of a massive cyberattack on a Puerto Rico government agency. Cybercriminals had gained access to the email account of an employee, understood to work in the Puerto Rico Employee Retirement System.
The compromised email account was used to send requests to other government agencies requesting changes be made to standard bank accounts for remittance payments. Since the email account used was trusted, the changes to bank accounts were made. Scheduled payments were then made as normal and millions of dollars of remittance payments were wired to attacker-controlled bank accounts.
The Puerto Rico Industrial Development Company, a state-owned corporation that drives economic development of the country, was one of the worst hit. Emails were received requesting changes to bank accounts and two payments were made. The first payment of $63,000 was made in December and another payment of $2.6 million in January. Other departments were also targeted, including the Tourism Company. The latter made a payment of $1.5 million. In total, the scammers attempted to steal around $4.73 million.
The business email compromise scam was uncovered when those payments were not received by the correct recipients. Prompt action was then taken to block the transfers and some of the payments were frozen, but the government has not been able to recover around $2.6 million of the stolen funds.
A full investigation has been launched to determine how the attackers gained access to the email account to pull off the scam. While the method used has not been confirmed, BEC attacks usually start with a spear phishing email.
A phishing email is sent to a person of interest requesting urgent action be taken to address a problem. A link is supplied in the email that directs the user to a website that requests their email account credentials. The account can then be accessed by the attacker. Attackers often set up mail forwarders to receive a copy of every email sent to and from the account. This enables them to learn about the company and typical payments and construct highly convincing scam emails.
Once access to a corporate email account is gained, the BEC scam is much harder to identify and block. The best defense is to ensure that the initial phishing emails are not delivered, and that is an area where TitanHQ can help.
by G Hunt |
February 12, 2020 |
Email Scams, Phishing & Email Spam
Emotet is the biggest malware threat faced by businesses and activity has increased considerably in recent weeks after a lull in December. Several new campaigns are now being identified each week, most of which are target businesses. One of the most recent campaigns uses a tried and tested technique to install the |Emotet Trojan. Malicious Word documents masquerading as invoices, estimates, renewals, and bank details.
The campaign mostly targets organizations in the United States and the United Kingdom, although attacks have also been detected in India, Spain, and the Philippines. Approximately 90% of emails in this campaign target financial services, with around 8% of attacks on companies in the food and drink industry.
The malicious Word documents are either attached to emails or hyperlinks are included in the emails that direct the user to a compromised website where the Word document is downloaded. The websites used are frequently changed and new Emotet variants are frequently released to prevent detection. Email security solutions that rely on AV engines to detect malware are unlikely to detect these zero-day threats as malicious.
Since Emotet is a massive botnet, emails spreading the Emotet Trojan come from many different sources. Email security solutions that rely on real-time blacklists are unlikely to detect these sources as malicious.
Emotet is primarily distributed via email from infected devices, but recently another distribution method has been identified. Emotet also spreads via Wi-Fi networks. This method has been used for almost two years, but it has only just been detected by security researchers at Binary Defense.
When Emotet is installed, a worm.exe binary is dropped that runs automatically. It attempts to connect to nearly Wi-Fi networks and brute forces weak passwords. Once connected to a Wi-Fi network, a search is conducted for non-hidden shares on the network. An attempt is made to enumerate all users connected to the Wi-Fi network, devices are brute forced, and the Emotet binary is dropped.
How to Block Emotet
The constantly changing tactics of the Emotet gang make detection difficult and no single solution will provide protection against all forms of attack. What is needed is a defense in-depth approach and layered defenses.
The primary defense against a predominantly email-based threat such as Emotet is an advanced spam filtering solution. Many businesses have used Office 365 and rely on the protection provided by Exchange Online Protection (EOP), which is included as standard with Office 365 licenses. However, EOP alone will not provide enough protection against Emotet. EOP will block all known malware threats, but it struggles to identify zero-day attacks. To block zero-day attacks, more advanced detection methods are required.
SpamTitan has been developed to work seamlessly with EOP to protect Office 365 email from zero-day threats. SpamTitan uses a variety of techniques to identify Emotet, including dual antivirus engines to block known Emotet variants and sandboxing to block zero-day attacks. Suspicious or unknown attachments are sent to the sandbox where they are subjected to in-depth analysis to identify command and control server callbacks and other malicious actions. SpamTitan also scans outgoing emails to identify attempts to spread Emotet from an already-infected machine. SpamTitan also incorporates DMARC to identify email impersonation and domain spoofing, which are commonly used in emails spreading Emotet.
To provide protection against the web-based element of attacks, including Emotet emails that use malicious hyperlinks rather than email attachments, another layer needs to be added to cybersecurity defenses – a DNS filtering solution such as WebTitan.
WebTitan uses real-time URL threat detection powered by 650 million end users. The real-time database includes more than 3 million malicious URLs and IP addresses and each day around 100,000 new malicious URLs are detected and blocked. WebTitan also includes real-time categorization and detection of malicious domains, full-path URLs, and IPs, with up-to-the-minute updates performed to block new malicious sources. As soon as a URL is identified as being used to distribute Emotet (or other malware) it is blocked by WebTitan. WebTitan also conducts link & content analysis, static, heuristic, & behavior anomaly analysis, and features in-house and 3rd party tools and feeds to keep users protected from web-based threats.
Other essential steps to take to tackle the threat from Emotet include:
- Disable macros across the organization
- Ensure operating systems are kept up to date and vulnerabilities are promptly patched.
- Set strong passwords to thwart brute force attacks
- Ensure endpoint protection solutions are deployed on all devices
- Provide security awareness training to employees
- Conduct phishing simulation exercises to identify employees that require further training
by G Hunt |
January 31, 2020 |
Email Scams, Phishing & Email Spam, Spam News
A novel coronavirus phishing campaign has been detected that uses scare tactics to trick users into infecting their computer with malware.
The World Health Organization has now declared the 2019 novel coronavirus outbreak a global emergency. The number of cases has increased 10-fold in the past week with almost 9,100 cases confirmed in China and 130 elsewhere around the world.
A worldwide health crisis such as this has naturally seen huge coverage in the press, so it is no surprise that cybercriminals are capitalizing on the concern and are using it as a lure in a malspam campaign to scare people into opening an email attachment and enabling the content.
A novel coronavirus phishing campaign has been detected that uses a fake report about the coronavirus to get email recipients to open a document that details steps that should be taken to prevent infection. Ironically, taking the actions detailed in the email will actually guarantee infection with a virus of a different type: Emotet.
The coronavirus phishing campaign was identified by IBM X-Force researchers. The campaign is targeted on users in in different Japanese prefectures and warning of an increase in the number of local confirmed coronavirus cases. The emails include a Word document attachment containing the notification along with preventative measures that need to be taken.
If the attachment is opened, users are told they must enable content to read the document. Enabling the content will start the infection process that will see the Emotet Trojan downloaded. Emotet is also a downloader of other malware variants. Other banking Trojans and ransomware may also be downloaded. Emotet can also send copies of itself to the victim’s contacts. Those messages may also be coronavirus related.
To add credibility, the Emotet gang makes the emails appear to have been sent by a disability welfare service provider in Japan. Some of the captured messages include the correct address in the footer.
More than 2,000 new infections have been confirmed in the past 24 hours in China and all of its provinces have now been impacted. Cases have now been reported in 18 other countries with Thailand and Japan the worst hit outside of China with 14 cases confirmed in each country. As the coronavirus spreads further and more cases are reported, it is likely that the Emotet gang will expand this campaign and start targeting different countries using emails in different languages. Kaspersky lab has also said that it has identified malspam campaigns with coronavirus themes that use a variety of email attachments to install malware.
Businesses can protect against Emotet, one of the most dangerous malware variants currently in use, by implementing a spam filtering solution such as SpamTitan that incorporates a sandbox where malicious documents can be analyzed in safety to check for malicious actions.
For further information on protecting your email system, contact TitanHQ today.
by G Hunt |
January 20, 2020 |
Email Scams, Phishing & Email Spam
Whenever there is a major event that attracts a lot of media attention cybercriminals will be poised to take advantage, so it is no surprise that warnings are being issued about Travelex phishing scams.
The Travelex ransomware attack that struck on New Year’s Eve involved a ransomware variant called Sodinokibi. The gang responsible is one of the most prolific threat groups using ransomware. The group’s attacks are highly targeted and seek to encrypt entire networks and the ransom demands reflect the scale of encryption. Travelex was initially issued with a demand for a payment of $3 million. That soon doubled to $6 million when payment was not made within the allocated timescale.
The fallout from the attack has been immense, which is unsurprising given that Travelex is the largest provider of currency exchange services worldwide. Many banks and retailers rely on Travelex to provide for their currency exchange services. Without access to those online services, currency exchange services came to a grinding halt. It has taken two weeks for Travelex to start bringing some of its services back online, but its website remains down and the disruption continues.
The attackers claimed to have stolen large quantities of customer data from Travelex. The attackers threatened to publish or sell the data if the ransom was not paid. This tactic is becoming increasingly common with ransomware gangs. In this case, the sodinokibi gang claimed to have gained access to Travelex systems 6 months previously and said they had stolen customer data including names, payment card information, and Social Security numbers and National Insurance numbers. The gang had also recently attacked the American IT company Artech Systems and had posted 337MB of data stolen in that attack, demonstrating to others that it was not an empty threat. Travelex maintained that no customer data had been stolen, but that has yet to be confirmed.
Warning Issued About Travelex Phishing Scams
Travelex customers should naturally err on the side of caution and monitor their accounts for signs of fraudulent use of their information but there are other risks from an attack such as this.
Travelex has issued a warning to its customers recommending they should be alert to the threat of phishing attacks via email and over the phone. Opportunistic scammers often take advantage of major events such as this and Travelex phishing scams are to be expected, as was the case following the TalkTalk data breach. These phishing scams are likely to be most effective on Travelex customers who have lost money as a result of the attack. Any offer of compensation or a refund is likely to attract a response.
For consumers, the advice is never to open email attachments or click on links in unsolicited emails. Businesses should also take steps to protect their networks from malware and phishing attacks.
Businesses should adopt a defense in depth strategy to protect against phishing scams and malware attacks. An advanced email security solution such as SpamTitan should be used to protect Office 365 accounts. SpamTitan improves protection against zero-day malware and phishing threats and blocks threats at the gateway.
A web filtering solution such as WebTitan should be used to block the web-based component of phishing and malspam campaigns and prevent end users from visiting malicious websites. End user training is also a must. It is important to teach employees how to identify phishing emails and malspam, and condition them how to respond when suspicious emails are received.
by G Hunt |
December 30, 2019 |
Email Scams, Phishing & Email Spam
Customers of Canadian banks have been targeted by cybercriminals in an extensive phishing campaign that has been ongoing for at least the past two years, according to Check Point Research which uncovered the campaign. As with many other financial phishing scams, the attackers spoof the website of a well-known bank and create a virtual carbon copy of the home page of the bank on a lookalike domain, which often only differs from the genuine domain name by a letter or two.
A link to the fraudulent site is then sent in a mass spamming campaign to email addresses on the specific country top level domain where the bank operates. The emails instruct users to visit the banks website and login, usually under the guise of a security alert. When the link in the email is clicked, the user is directed to the spoofed site and may not notice the domain name is not quite right. They then enter their login credentials which are captured by the scammers. The credentials are then used to make fraudulent wire transfers to accounts controlled by the attackers.
In this campaign, the emails include a PDF email attachment. PDF files tend to be trusted to a higher degree than Word documents and spreadsheets, which end users have usually been instructed to treat as suspicious. The PDF file includes a hyperlink, which the user is instructed to click. Since the hyperlink is in the document rather than the email body, it is less likely to be scanned by email security solutions and has a higher chance of being delivered.
The user is told that they are required to update their digital certificate to continue using the online banking service. The PDF file includes the bank logo and a security code, which the user is required to enter when logging in. The code is included in the PDF attachment rather than email body for security reasons. As with most phishing scams, there is urgency. The recipient is told that the code expires in 2 days and that they must register within that time frame to avoid being locked out of their account.
The landing pages on the websites are identical to those used by the banks as the attackers have simply taken a screen shot of the bank’s landing page. Text boxes have been added where the username, password, and token number must be entered. Users are then asked to confirm the details they entered while the attackers attempt to access their account in real-time and make a fraudulent transfer.
These tactics are nothing new. Scams such as this are commonplace. What is surprising is how long the campaign has been running undetected. The scammers have been able to operate undetected by registering many lookalike domains which are used for a short period of time. Hundreds of different domains have been registered and used in the scam. At least 14 leading banks in Canada have had their login pages spoofed including TD Canada Trust, Scotiabank, Royal Bank of Canada, and BMO Bank of Montreal.
All of the websites used in the scam have now been taken down, but it is all but guaranteed that other lookalike domains will be registered and further scams will be conducted.
by G Hunt |
December 27, 2019 |
Email Scams, Phishing & Email Spam
A spamming campaign has been detected that is piggybacking on the popularity of Greta Thunberg and is using the climate change activist’s name to trick individuals into installing the Emotet Banking Trojan.
Emotet is one of the most active malware threats. Emotet was first detected in 2014 and was initially used to steal online banking credentials from Windows users by intercepting internet traffic. Over the years it has undergone several updates to add new functionality. It has had a malspam module added, which allows it to send copies of itself via email to a user’s contacts. Emotet also includes a malware downloader, allowing it to download a range of other malware variants such as other banking Trojans and ransomware.
The malware is used indiscriminately in attacks on individuals, businesses, and government agencies, with the latter two being the main targets. Emotet is primarily spread via spam email, and while exploits are not used to spread to other devices on the network – EternalBlue for instance – other malware variants downloaded by Emotet can. TrickBot for instance.
The Greta Thunberg spam campaign aims to get users to open a malicious Word attachment and enable content. If that happens, Emotet will be silently downloaded to the user’s device, sensitive banking information will be stolen, and further malware may be downloaded.
The campaign was active over the holiday period and used a variety of Christmas-themed lures to entice users into opening the email attachment. Some of the emails did not include an attachment and instead used a hyperlink to direct the user to a website where the malicious document could be downloaded.
One of the emails wished the recipient a Merry Christmas and urged them to consider the environment this Christmastime and join a demonstration in protest against the lack of action by governments to tackle the climate crisis. The email claimed details about the time and location of the protest were included in the Word document. The email also requested the recipient to send the email on to all their colleagues, friends, and relatives immediately to get their support as well. Several variations along that theme have been detected.
To increase the likelihood of the recipient enabling content, when opened the document displays a warning that appears to have been generated by Microsoft Office. The user is told that the document was created in OpenOffice and it is necessary to first enable editing first and then enable content. Doing the latter will enable macros which will start the infection process.
The emails are well written and have been crafted to get an emotional response, which increases the likelihood of the user taking the requested action. The emails have been sent in multiple languages in many different countries.
Whenever there is a major news event, popular sports tournament, or other event that attracts global interest, there will be cybercriminals taking advantage. Regardless of the theme of any email, if it is unsolicited and asks you to click a link or open an email attachment, it is best to assume that it is malicious.
Businesses can protect their networks against threats such as these by implementing an advanced spam filtering solution such as SpamTitan. SpamTitan will identify threats such as phishing attacks and will prevent the messages from reaching inboxes. SpamTitan also includes dual anti-virus engines to detect known malware and machine learning techniques and sandboxing to identify and block zero-day malware.
For further information on how SpamTitan can protect your business from email threats such as this, contact TitanHQ today.
by G Hunt |
November 27, 2019 |
Phishing & Email Spam
A new phishing campaign has been detected that is targeting Office 365 admins, whose accounts are far more valuable to cybercriminals than standard Office 365 accounts.
A standard Office 365 email account can used for spamming or conducting further phishing attacks on the organization or business contacts. However, there is a problem. When the account is used for phishing, the sent messages are likely to be noticed by the user. Failed delivery messages will also arrive in the user’s inbox. The account may only be able to be used for a short time before an account compromise is detected.
The attackers targeting Office 365 admins aim to compromise the entire domain. Office 365 admins can create new accounts on the domain, which are then used for phishing. Since the only person using that account is the attacker, it is likely the malicious actions will not be noticed, at least not as quickly. The only person who will see the failed delivery messages and sent emails is the attacker.
The newly created account abuses trust in the business domain. Any individual to receive such a phishing message may mistakenly believe the email is a legitimate message from the company. The messages also take advantage of the reputation of a business. Since the business domain will have been used only to send legitimate messages, the domain will have a high trust score. That makes it far more likely that the emails being sent from the new account will be delivered to inboxes and will not be picked up by Office 365 spam filters. The Office 365 admin may also have access to all email accounts on the domain, which will allow the attacker to steal a huge amount of email data.
In theory, Office 365 admins should be better at identifying phishing emails than other employees in the organization as they usually work in the IT department; however, these emails are very realistic and will likely fool many Office 365 admins.
The lure being used is credible. The emails appear to have been sent by Microsoft and include the Microsoft and Office 365 logos. The emails claim that the organization’s Office 365 Business Essentials invoice is ready. The user is told to sign into the Office 365 admin center to update their payment information, set their Message Center preferences, and edit their release preferences or join First Release and set these up if they have not done so already. The emails include an unsubscribe option and are signed by Microsoft and include the correct contact information. The emails also link to Microsoft’s privacy statement.
The embedded hyperlinks in the emails link to an attacker-controlled domain that is a carbon copy of the official Microsoft login page. If the user’s credentials are entered, they are captured by the attacker.
This campaign highlights how important it is to have layered email security defenses in place to block phishing attacks. Many phishing emails bypass standard Office 365 anti-phishing controls so additional protection is required.
An advanced anti-phishing solution such as SpamTitan should be layered on top of Office 365 to provide greater protection against sophisticated phishing attacks. Approximately 25% of all phishing emails bypass standard Office 365 phishing protections.
Another anti-phishing layer that many businesses have yet to implement is a web filter. A web filter, such as WebTitan, provides protection when messages are delivered to inboxes, as it blocks attempts by employees to visit phishing websites. When a link to a known phishing website is clicked, or the user attempts to visit a questionable domain, they will be directed to a block page and the phishing attack will be blocked.
by G Hunt |
May 9, 2017 |
Phishing & Email Spam
A Sabre Corporation data breach has potentially resulted in the theft of credit card details and PII from the SynXis Hospitality Solutions reservation system. The Sabre Corporation data breach was acknowledged in Sabre Corp’s Q2 10-Q filing with the Securities and Exchange Commission. Few details about the security incident have been released as the incident is currently under investigation.
What is known is the incident affects SynXis, a cloud-based SaaS used by more than 36,000 independent hotels and global hotel chains. The system allows employees to check room availability, pricing and process bookings.
Sabre Corporation recently discovered an unauthorized third party gained access to the system and potentially viewed the data of a subset of Sabre Corp’s hotel clients. Information potentially compromised as a result of the Sabre Corporation data breach includes the personally identifiable information and payment card information of hotel guests.
At this stage, Sabre Corporation is still investigating the breach and has not disclosed how the individual gained access to the payment system or when access was first gained. Sabre Corp is currently trying to determine exactly how many individuals have been affected, although affected companies have now been notified of the incident.
Sabre Corp has confirmed that the security breach only affected its SynXis Central Reservations system and unauthorized access has now been blocked. Law enforcement has been alerted to the incident and cybersecurity firm Mandiant contracted to conduct a full forensic investigation of its systems.
The Sabre Corporation data breach is the latest in a string of cyberattacks on hotel chains. Hyatt Hotels Corp, Kimpton Hotels and Restaurants, Omni Hotels & Resorts, Trump Hotels, Starwood Hotels & Resorts, Hilton Hotels, HEI Hotels & Resorts and InterContinental Hotels Group have all experienced data breaches in recent months that have resulted in the attackers gaining access to their card payment systems.
While the method used to gain access to Sabre’s system is not yet known, similar cyberattacks on hotel reservation and payment systems have involved malware and compromised login credentials.
If malware is installed on systems it can be used to monitor keystrokes and record login credentials. The sharing of login credentials and poor choices of passwords can also allow attackers to gain access to login credentials.
To protect against cyberattacks, hotels and their contracted SaaS providers should use layered defences including multiple systems to prevent the downloading of malware and multi-factor authentication to reduce the risk from compromised login credentials being used to gain access to POS systems.
Web filters should be used to control employees’ Internet access and downloads, an antispam solution used to prevent malicious emails from reaching end users’ inboxes and anti-virus and anti-malware solutions should be kept up to date and set to scan networks regularly.
Organizations in the hospitality sector must also ensure they have the basics correct, such as changing default passwords, using strong passwords and employing good patch management policies.
by G Hunt |
March 6, 2017 |
Phishing & Email Spam
A recently published study from the Federal Trade Commission’s (FTC) Office of Technology Research and Investigation has revealed that anti-phishing technologies are not being widely adopted by U.S. businesses.
While there are several anti-phishing technologies that could be adopted by businesses to reduce susceptibility to phishing attacks, relatively few businesses are taking full advantage of the latest anti-phishing solutions.
Phishing is a type of online scam primarily conducted via email, although the same type of scam can occur online on malicious websites. The email version of the scam involves sending an email request to an employee in which the attacker claims to be a well-known source. That could be an Internet service provider, a well-known company such as Amazon or Netflix, or the CEO or CFO of the employee’s company. The target is asked to send sensitive personal or business information.
Typically, the attackers request financial information, logins, or as we have seen on numerous occasions this year, employees’ W-2 Form data. The information is then used for identity theft and fraud. In the case of the W-2 Form phishing scams, the information is used to file fraudulent tax returns in employees’ names.
Phishing is one of the biggest cybersecurity threats that businesses must mitigate. A separate study conducted by PhishMe showed that the vast majority of cyberattacks start with a phishing email. The largest ever healthcare data breach – which resulted in the theft of 78.8 million health insurance members’ credentials from Anthem Inc. – occurred as a result of an employee responding to a phishing message.
The FTC’s research revealed that most businesses have now implemented authentication controls, but little else. The FTC study (performed by OTech) found that 86% of businesses were using the Sender Policy Framework (SPF) to determine whether emails that claim to have been sent from a business were actually sent from the domain used by that business.
While this is an important anti-phishing control, SPF alone is insufficient to protect businesses from phishing attacks. SPF controls can be bypassed.
The FTC study found that fewer than 10% of businesses were using Domain Message Authentication Reporting & Conformance (DMARC) to receive intelligence on the latest spoofing attempts used to bypass SPF controls. DMARC allows businesses to automatically reject unauthenticated messages, yet few use the technology.
While not covered by the FTC study, one of the best additional anti-phishing technologies is a spam filtering solution such as SpamTitan.
SpamTitan blocks 99.97% of spam email messages, 100% of known malware via its dual anti-virus engines, while a powerful anti-phishing component looks for common signatures of phishing emails and prevents them from being delivered.
The threat from phishing is growing. A study from the Anti-Phishing Working Group revealed there was a 65% increase in phishing attacks in 2016 compared to 2015. Last year, 1,220,523 phishing attacks were reported. With attacks increasing at such a rate, and given the number of phishing attacks on businesses so far in 2017, more must be done to prevent attacks.
Is your business doing enough to prevent phishing attacks? What anti-phishing technologies has your business adopted to prevent employees being scammed?
by G Hunt |
December 13, 2016 |
Phishing & Email Spam
All antispam solutions and spam filters check inbound messages for common spam signatures; however, it is also important to choose a solution that performs outbound email scanning. Outbound email scanning ensures spam emails, or emails containing malware, are not sent from an organization’s email accounts or domains.
Your employees would be unlikely to knowingly use their corporate email accounts to send spam emails, but malware infections can allow cybercriminals to gain access to email accounts and use them to send high volumes of spam email messages. Cybercriminals could also compromise email accounts and use an organization’s domain to send malware and ransomware to clients and customers.
Should this happen, it can have a seriously detrimental effect on an organization’s reputation and may result in corporate email accounts or an entire domain being blacklisted.
Blacklists are maintained by a number of organizations – spamhaus.org for example. Internet Service Providers (ISPs), web servers, and antispam solutions check these blacklists before allowing emails to be delivered to end users. If a particular IP address, email account, or domain is listed in one of the blacklist databases, emails sent from the domain, IP address or email account will not be delivered.
Blacklists are updated in real-time and contain many millions of blocked domains and email addresses that have been reported as having been used for unwanted activity such as the sending of spam emails. If emails are sent from a blacklisted account, domain, or IP address those emails will either be directed to a quarantine folder, deleted, or will simply be rejected.
If a business has its domain added to a spam blacklist important emails to clients and customers will not get through. This can prove costly, as real estate firm Keller Williams has recently discovered.
Blacklisted Domains and Email Accounts Can Prove Costly for Businesses
Over the past few days, email messages sent from the kw.com domain used by Keller Williams have been rejected by AOL. Yahoo has been blocking emails from the kw.com account for some time. The problem appears to be the addition of the kw.com domain to spam blacklists.
If a Keller Williams real estate agent needs to send an email to a customer who has an AOL or Yahoo account, it will not be delivered. Agents have therefore been forced to get customers to open Google email accounts in order to send online paperwork or documents requiring e-signatures.
The issue also affects online paperwork sent via the transaction management software program Ziplogix, with one Keller Williams agent also claiming Dotloop is also affected. Some agents at Keller Williams have reportedly had to send important paperwork for listings and sales via personal email accounts to ensure emails are delivered.
The AOL website explains that when domains have been flagged as being abusive, the server will be temporarily blocked until the spamming stops. Until a domain is removed from its blacklist, AOL account holders will be prevented from receiving emails from the blocked domain. Removing the domain from the blacklist can take up to a week.
Removing a domain from the 80+ commonly used spam blacklists can be a time-consuming task; furthermore, if spam emails are sent from the account again, the domain will simply be added to the blacklists once more.
Outbound Email Scanning Prevents the Blacklisting of an Organization’s Domain
Unlike many third-party antispam solutions, SpamTitan checks incoming email messages for spam signatures as well as performing outbound email scanning. If an email account has been compromised and is being used to send spam emails, if malware is sending spam, those messages will be blocked and will not be sent. Outbound email scanning is an important protection that will prevent an organization’s domain or email accounts from being used to send spam or malware.
Organizations can therefore avoid the embarrassment and reputation damage that results from being suspected as engaging in spamming or malware delivery. They can also rest assured that in addition to blocking 99.97% of inbound email spam, their domains and email accounts will not be added to spam blacklists.
by G Hunt |
December 2, 2016 |
Phishing & Email Spam
‘Tis the season to be jolly, although ‘tis also the season to be infected with malware. The holiday season is an annual highlight for cybercriminals. Holiday season malware infections are to be expected as cybercriminals increase their efforts and try to infect as many users with malware as possible.
Malware is an ever-present threat, but the increase in online activity in the run up to the holiday season means easy pickings for cybercriminals. Consumers are starting to prepare for the holidays earlier, but not as early as the scammers. As consumers head online in their droves, scammers and other cybercriminals are lying in wait.
The advent of Black Friday and Cyber Monday – days where shoppers are offered amazing deals to prompt early Christmas purchases– see a frenzy of online activity. There are discounts aplenty and great deals to be had.
However, not all of those discounts are genuine. Many are scams that are used to phish for sensitive information or spread malware infections. As is the case every year, the holiday season sees a spike in malware infections, with the biggest spike over Thanksgiving weekend. This year has been no exception. Holiday season malware infections have increased significantly year on year.
Holiday Season Malware Infections Rise 118% Above Normal Levels
This year, over the first official shopping weekend of the holiday season, malware infections increased by 106% according to data compiled by the Enigma Software Group. On Cyber Monday, when even more great deals on online purchases are made available, malware infections were 118% higher than normal.
Those figures are only for Windows users. Add in smartphones and Apple devices and the figures would be higher still. The problem is also getting worse. Last year there was a spike of 84% over normal levels during the Thanksgiving weekend.
There have been a number of suggestions put forward as to why the figures are so high this year. One of the main reasons is simply due to the number of shoppers heading online. Each year sees more individuals choosing to go online shopping over Thanksgiving weekend. More online shoppers mean more opportunities to infect users with malware.
However, there are also more actors involved in online scams, malware-as-a-service and ransomware-as-a-service has also grown in popularity, and many cybercriminals have started up affiliate schemes to get more help spreading their malicious software. Individuals who succeed in infecting computers with ransomware are given a cut of the profits and there is no shortage of people willing to try the affiliate schemes to boost their own earnings.
Cybercriminals are also getting better at developing convincing scams and malicious email messages. The grammatical and spelling mistakes that were common in phishing emails in years gone by are largely gone. Now, almost perfect emails are sent and scammers are using a wide range of social engineering techniques to lure end users into clicking on malicious links or opening infected email attachments. Spoofed retail sites are also now commonplace – and extremely convincing.
The growth of social media has also helped boost cybercriminal activity. Malicious posts are being shared online offering discounts, special offers, and unmissable deals. However, all end users get is a malware download.
Avoiding a Bad Start to Holiday Season
To avoid becoming a victim of a scam or having to deal with a malware or ransomware infection, shoppers must be vigilant and exercise more caution. Offers that sound too good to be true usually are. Unsolicited emails should always be treated as suspicious and extra care should be taken when clicking on any link or visiting a retail site.
Businesses should also take extra precautions. A malware or ransomware infection can prove extremely costly to resolve. While warnings should be sent to end users about the risks of holiday season malware infections, technological solutions should also be in place to prevent malicious file downloads.
Antispam solutions are highly effective at blocking malicious messages such as phishing emails and emails containing malware. SpamTitan blocks 99.97% of spam messages, contains a powerful anti-phishing module, and blocks 100% of known malware.
Malicious links on social media sites and on third-party ad networks (malvertisting) are a very real risk. However, a web filter can be used to control access to social media sites, block malicious third-party adverts, and prevent end users from visiting websites known to contain malware.
If you want to keep your network free from malware this holiday season, if you have not already used these two solutions, now is the time. They will also help to keep your network malware free around the year. And with security experts predicting a massive increase in ransomware and malware attacks in 2017, there is no better time to start improving your defenses.
by G Hunt |
November 30, 2016 |
Phishing & Email Spam
The Federal Trade Commission (FTC) in the United States has responded to the current ransomware epidemic by issuing ransomware advice for businesses and consumers. The FTC ransomware advice for businesses comes following a spate of high profile ransomware attacks on U.S businesses. The threat has prompted many U.S. government agencies to release ransomware advice for businesses in the past few months.
Ransomware is a form of malware that encrypts files on a victim’s computer and prevents them from being accessed. After a computer is infected, the attackers issue a ransom demand. In order to obtain the key to unlock the encryption the victim is required to pay a ransom. The ransom amount can be set by the attackers, although it is often around $500 per infected computer.
Ransomware has proved incredibly popular with cybercriminals as it offers a quick source of revenue. Since payment is made in an anonymous cryptocurrency such as Bitcoin, money can be collected without fear of being caught.
The scale of the problem has been shown by numerous reports by security firms. This month, SentinelOne released the results of a global survey that showed 48% of organizations had experienced at least one ransomware attack in the past 12 months. The companies that had been attacked had been forced to deal with an average of 6 ransomware incidents in the past year.
A report released by Beazley’s Breach Response Unit suggests ransomware attacks between January and September were four times higher than in 2015, while a report from Kaspersky Lab suggests there has been an eightfold increase in attacks in the past year.
Ransomware is installed via a number of different attack vectors. Ransomware gangs use exploit kits on websites that probe for vulnerabilities in browsers. Those vulnerabilities are leveraged to download ransomware. Malvertising is also used. This is the use of third party ad networks to spread malware. Adverts are created containing malicious code which directs users to websites that silently download ransomware. Ransomware downloaders were also allegedly sent out via Facebook Messenger this week.
However, the biggest attack vector is email. Spam emails are sent containing attachments that have been infected with malicious macros, JavaScript files, and other ransomware downloaders. Links to malicious websites are also distributed via email. The attackers use a range of social engineering techniques to convince email recipients to click on malicious links or open infected attachments. Doing so results in ransomware being installed.
While not all ransomware attacks result in files being encrypted, attacks carry a significant cost. SentinelOne suggests that in the United States, organizations spend an average of 38 man-hours restoring files from backups after a ransomware attack. Additional investment in security is also required after an attack.
Since ransomware can spread laterally across a network, a single infection can result in many computers being infected. Ransom demands of the order of tens of thousands of dollars are not uncommon. The recent ransomware attack on the San Francisco ‘Muni’ rail system saw a ransom demand of $73,000 issued.
Ransomware Advice for Businesses
Unfortunately, antivirus software can be ineffective at preventing ransomware attacks. Businesses looking to defend against ransomware must therefore use a range of techniques. These include:
- Ensuring all software is kept up to date and patches applied promptly
- Setting antivirus and antimalware programs to update definitions automatically
- Use endpoint security controls to prevent ransomware installations
- Implement a robust spam filter to prevent malicious emails from being delivered to end users
- Use a web filtering solution to prevent employees from visiting malicious websites and to monitor users’ online activities to identify high risk activities
- Use intrusion prevention software
- Train the workforce on security best practices and test knowledge to ensure training has been effective
- Ensure all members of staff are aware who to contact and what to do if they believe they have inadvertently installed malicious software
To avoid paying a ransom, it is essential to ensure that regular backups of data are performed. Multiple backups should be made to minimize the risk of data loss. Those backups should be stored on an air-gapped device to avoid backup files also being encrypted. A ransomware response plan should also be developed to reduce disruption to the business in the event of an attack.
by G Hunt |
August 31, 2016 |
Phishing & Email Spam
The use of Word macros and malicious JavaScript to deliver malware is nothing new; however, Microsoft has recently discovered that malicious actors are using malicious OLE embedded scripts to deliver a different payload. The discovery had prompted the software giant to issue a warning to Windows users to alert them to the risk.
Attackers are using the MS Office object linking and embedding (OLE) function to insert malicious scripts into spam emails. Social engineering techniques are also used to encourage users to double click on the malicious OLE embedded scripts.
The spam email messages used for these campaigns are simplistic, but effective. They appear to contain an invoice or receipt in the form of an attached Word document. However, the document contains a malicious JS script called Trojan:JS/Certor.A. Running the script will result in the users’ proxy settings being changed which will allow the attackers to steal authentication credentials and other sensitive data.
Opening the attached Word document will not automatically result in a user’s computer being compromised. The attached documents contain malicious OLE embedded scripts which are masked by text or icons. Typically, these embedded objects contain text asking the user to double click to view the invoice or receipt.
If the user double clicks as requested, they will receive a security warning on screen asking for confirmation that they want to open the file. The file will be identified as a Jscript Script file, but it will have an innocuous name. The user may not realize that the file is malicious. Although the names of the file are different for each campaign, they typically include terms such as PayPal, invoice, or receipt.
Allowing the file to be opened will see a range of malicious functions executed. Registry keys related to browser proxy settings will be modified, and a number of components will be dropped and executed. The malware even carries its own certificate.
The malware can be used to redirect users to malicious websites containing exploit kits, phishing campaigns, or ads. However, the malware will also enable the attackers to monitor HTTPS content and traffic and steal sensitive data such as login credentials entered on secure websites. The end user will be unaware that their computer has been compromised and that their actions online are being monitored.
To avoid infection, users have been told not to open attached files that are sent from unknown senders. Microsoft also says that this advice is all too often ignored by end users. For large businesses with many employees, preventing all users from running malicious OLE embedded scripts is a problem. There is always one employee that ignores security best practices. Unfortunately, all it takes for a network to be compromised is for one employee to run a malicious script.
The best step to take to ensure this doesn’t happen is to use a powerful spam filtering solution such as SpamTitan. SpamTitan stops 99.97% of spam emails from being delivered to end users’ inboxes.
Additionally, to prevent malicious OLE embedded scripts from being run, Microsoft offers the following advice:
“For added defense-in-depth, you can reduce the risk from this threat by following [Microsoft] guidance to adjust the registry settings to help prevent OLE Embedded Objects executing altogether or running without your explicit permission.”
by G Hunt |
June 28, 2016 |
Phishing & Email Spam
A new Microsoft Office 365 zero day vulnerability is being exploited by hackers to deliver Cerber ransomware. The latest attack is being conducted on a large scale and it has been estimated that millions of business users have already been impacted by the latest Cerber ransomware campaign.
It can be difficult to keep up to date with all of the ransomware variants currently being used by cybercriminals. The malicious file-encrypting software is constantly being tweaked and reinvented by cybercriminals. Cerber ransomware especially. The criminals behind Cerber frequently change its attack mode.
Cerber was first seen in February this year and has already been delivered using a variety of methods, most recently via the Dridex botnet. Spam emails containing malicious Word macros has been favored in the past. If allowed to run, the macros would download Cerber onto victims’ devices. Cerber would then proceed to encrypt documents, images, and a host of other file types.
Victims would be presented with a warning message on screen alerting them to the infection, and an audio file would be played to chilling effect. Cerber was unique in this respect, essentially speaking to its victims. Cerber has also been delivered using malvertising – advertisements placed in third party ad networks that direct web visitors to malicious webpages hosting exploit kits. Those exploit kits probe for browser and plugin vulnerabilities which are exploited to deliver the ransomware. That campaign mainly infected users that had failed to keep their Flash plugins up to date.
It is the rapid changes being made by the attackers that has made it so difficult to detect Cerber and prevent infections. Earlier this month, Invincea discovered that Cerber was able to manufacture new payload variants “on the fly”, allowing the attackers to bypass traditional signature-based anti-virus products. Unique hashes and payloads were being generated every 15 seconds! In tests, 40 unique hashes were discovered.
Cerber Ransomware is Now Infecting Users via Microsoft Office 365 Zero Day Vulnerability
The latest attack has bypassed many users’ anti-virus products according to security firm Avanan. It is unclear at this stage exactly how many organizations have been affected, although Avanan reports that 57% of its clients that use Office 365 have been hit.
Users who have not implemented additional email security controls have been infected via their cloud email accounts. The latest attack is bypassing the controls put in place by Microsoft and the spam emails are being delivered to end user accounts. Unfortunately, should Cerber ransomware be installed, the victims will have to recover the encrypted files from backups or pay the ransom.
The criminals behind the latest campaign may currently be exploiting the Microsoft Office 365 zero day vulnerability, but we can be sure that Cerber will continue to evolve.
To protect against Cerber ransomware attacks, business users must ensure that all patches and software updates are applied promptly.
Since ransomware is capable of infecting or deleting back up files, it is essential that backup devices are air gapped. When backups have been performed, the drives need to be disconnected.
Implementing an anti-spam solution – and not relying on Microsoft or Gmail anti-spam filters – can also help to keep businesses protected by reducing the risk of ransomware and other phishing emails from being delivered to end users.
by G Hunt |
June 4, 2016 |
Phishing & Email Spam
The latest phishing email statistics released by the anti-phishing training company PhishMe show the extent to which the use of phishing has increased in recent months.
PhishMe compiles quarterly phishing email statistics and tracks the volume of phishing emails being sent. During the first three months of 2016, the volume of phishing emails increased by a staggering 789%. More than 6.3 million more phishing emails were sent in Q1, 2016 than in Q4, 2015.
According to the quarterly report, the biggest problem currently faced by personal and corporate computer users is ransomware. Ransomware emails now account for more than 93% of all phishing emails. Ransomware offers a quick payout for cybercriminals and the campaigns can be quickly developed and run. In fact, ransomware emails are being sent by criminals with little or no programming skill. They can simply purchase ransomware kits on darknet marketplaces and obtain a cut of the ransom payments that are made.
Targeted ransomware attacks are now being conducted on businesses of all sizes. Criminals are well aware that many organizations do not regularly perform backups of critical data. Even when backups are performed, many organizations do not unplug their backup devices. The latest ransomware variants are capable of deleting Windows shadow copies and encrypting backup files on connected storage devices. This gives organizations no alternative but to pay the ransom demand to recover files. The biggest threat is now Locky. Locky is delivered via spam email using JSDropper or malicious Word macros.
PhishMe’s phishing email statistics also show two other main trends. Cybercriminals are tending to concentrate on soft-targeted campaigns. Spear phishing emails target just one or two individuals, but the latest trend sees malicious emails messages sent to a group of individuals in an organization – the billing department for instance. The emails are targeting specific roles in an organization rather than specific individuals.
The phishing email statistics also show a rise in the use of JSDropper applications. JSDropper applications are now present in around a third of all phishing emails. Malicious Word macros are still extensively used to infect computers with malware and ransomware, but JavaScript applications are now the most common type of malicious files sent in phishing emails according to the report.
The increase in malicious spam email shows how important it is for organizations to employ a robust spam filtering solution – SpamTitan for example – and to also ensure that employees are informed of the high risk of phishing attacks occurring. Employees should also be instructed how to identify phishing emails and told how they should respond if they believe they have been sent a malicious email message.
by G Hunt |
December 22, 2015 |
Phishing & Email Spam
A new Lloyds Bank phishing scam has been uncovered. The UK bank’s customers are being targeted just before Christmas with a highly realistic email, apparently sent from Lloyds Banking Group. Christmas is a time when people let their guard down. Its busy at work, there is much to do, and minds are invariably on Turkey, holidays, and rushing to get last minute preparations completed.
New Lloyds Bank phishing scam is highly realistic
The email contains the exact same font, logo, and styling that are used on the real online banking portal, making the campaign one of the most realistic online banking phishing scams we have seen.
The latest Lloyds Bank phishing scam is pure simplicity. It is brief and to the point, and has been designed to scare users into clicking on the link and signing into their account to check their bank balance.
All that the email says, is “You have One New Message. Your account has been accessed in multiple locations. Click below to update your Lloyds Bank Account, with a hyperlink using the anchor text “Sign In.” There are no spelling mistakes or grammatical errors to warn users that the email is anything but genuine.
In fact, even clicking the sign in link is unlikely to arouse suspicion. The link will direct the soon-to-be victim to a website containing an exact copy of the Lloyds Bank portal that customers will be very familiar with. All of the text is genuine, and the website features apparently clickable links in all the right places. It is an almost exact replica of the real site.
Only if a user decides to click on any of the links will they realize something is not quite right. The scammers have only taken an image of the real site. They have not made any of the links actually clickable.
But then again, after the recipient of the email has been sent a warning telling them their account is under threat, they are unlikely to suddenly decide to check the latest mortgage rates or take out a loan.
The only part of the website that works is the section where users are required to enter their user ID, password, and memorable word. Once the credentials have been entered, the victim will be redirected to Lloyds. That may arouse suspicion when their login attempt did not work, but the scammers hope that few will bother to change their password when they realize their account has not been compromised.
The scammers are likely to act quickly. Once they have a User ID, password, and memorable word, they have the basic information necessary to access the account. That information may be sufficient to gain access to the account and make a fraudulent transfer. If not, it will be used as the basis for a further spear phishing email to attempt to get the answer to a security question. If the victim fell for the first campaign, chances are they will fall for another.
There is only one other giveaway that this is a Lloyds Bank phishing scam. The URL is not lloydsbank.com.
The scam highlights the importance of checking the URL before entering any login credentials and checking to make sure the site address starts with https://. This site is clearly not genuine and has no green padlock, indicating something is amiss to anyone even casually checking the web address. However, not all online banking customers will do that when the website appears to look like the real deal.