by titanadmin | Sep 20, 2017 | Email Scams, Network Security, Phishing & Email Spam, Spam News, Spam Software |
A new spam email ransomware campaign has been launched that has potential to infect users twice, with both Locky and FakeGlobe ransomware.
The campaign, which was launched earlier this month, sees the attackers alternate the payload between Locky and FakeGlobe ransomware. The researchers that discovered the campaign suggest the payload alternates each hour.
This method of distribution cpould result in victims being infected twice, first having their files encrypted by Locky ransomware, and then re-encrypted by FakeGlobe ransomware or vice versa. In such cases, two ransom payments would have to be paid if files could not be recovered from backups.
While the use of two malware variants for spam email campaigns is not new, it is much more typical for different forms of malware to be used, such as pairing a keylogger with ransomware. In such cases, if the ransom is paid to unlock data, the keylogger would likely remain and allow data to be stolen for use in further attacks.
As with previous attacks involving Locky, this double ransomware campaign involves fake invoices – one of the most effective ways of getting business users to open infected email attachments. In this campaign, the attachment claims to be the latest invoice which takes the form of a zip file. Opening that zip file and clicking to open the extracted file launches a script that downloads the malicious payload.
The emails also contain a hyperlink with the text “View Your Bill Online,” which will download a PDF file containing the same script as the attachment, although it connects to different URLs.
This campaign is widespread, being distributed in more than 70 countries with the large-scale spam campaign involving hundreds of thousands of messages.
Infections with Locky and FakeGlobe ransomware see a wide range of file types encrypted and there is no free decryptor to unlock the infections. Victims must either restore their files from backups or pay the ransom to recover their data.
If businesses are targeted, they can easily see multiple users fall for the campaigns, requiring multiple computers to be decrypted. However, since ransomware can spread across networks, all it takes is for one user to be fooled into downloading the ransomware for entire systems to be taken out of action. If data cannot be recovered from backups, multiple ransom payments will need to be made.
Good backup policies will help protect businesses against file loss and prevent them from having to pay ransoms; although, even if backups exist, organizations can experience considerable downtime while the malware is removed, files are restored, and networks are analyzed for other malware infections and backdoors.
Spam email remains the vector of choice for distributing ransomware. Organizations can reduce the risk of ransomware attacks by implementing an advanced spam filter such as SpamTitan. SpamTitan blocks more than 99.9% of spam emails, preventing malicious emails from reaching end users’ inboxes.
While most organizations are now using spam filtering software to prevent attacks, a recent study conducted by PhishMe suggests 15% of businesses are still not using email gateway filtering, leaving them at a high risk of ransomware attacks. Given the volume of phishing and ransomware emails now being sent, email filtering solutions are a necessity.
by titanadmin | Sep 20, 2017 | Internet Security, Network Security |
CCleaner malware infections continued for a month before the compromised binary was detected and the backdoor was removed.
Avast, which acquired Piriform over the summer, announced that between August 15 and September 15, a rogue version of the application was available on its server and was being downloaded by users. During that time, around 3% of users of the PC cleaning application had been infected according to Piriform.
Cisco Talos, which independently discovered the build of CCleaner had malware included, reported around 5 million users download the program each week, potentially meaning up to 20 million users may have been affected. However, Piriform suggests around 2.27 users had downloaded and installed the backdoor along with the legitimate application. On Monday this week, around 730,000 users had not yet updated to the latest, clean version of the program.
Any individual that downloaded the application on a 32-bit system between August 15 and September 15 was infected with the CCleaner malware, which was capable of gathering information about the users’ system. The malware in question was the Floxif Trojan, which had been incorporated into the build before Avast acquired Piriform.
The CCleaner malware collected details of users’ IP addresses, computer names, details of software installed on their systems and the MAC addresses of network adaptors, which were exfiltrated to the attackers C2 server. The CCleaner malware laced application was only part of the story. Avast says the attack involved a second stage payload, although it would appear the additional malware never executed.
The versions of the software affected were v5.33.6162 and CCleaner Cloud v1.07.3191. The malware reportedly did not execute on 64-bit systems and the Android app was unaffected. The malware was detected on September 13, 2017, although an announcement was not initially made as Avast and Piriform were working with law enforcement and did not want to alert the attackers that the malware had been detected.
The individuals behind the attack used a valid digital signature that was issued to Piriform by Symantec along with a Domain Generation Algorithm to ensure that new domains could be generated to receive exfiltrated data from compromised systems in the event that the main domain was taken down.
Now that the malware has been removed, users can simply download version 5.34 of the application which will remove the backdoor. Users of the Cloud version need do nothing, as the application has been updated to a clean version automatically. While simply updating the software should resolve all issues, users are advised to perform a full virus scan to make sure no additional malware has been introduced onto their system.
At present, it is unclear who was responsible for this supply chain attack or how the Floxif Trojan was introduced. It is possible that external hackers gained access to the development or build environment or that the Trojan was introduced from within.
Attacks such as this have potential to infect many millions of users since downloads from the developers of an application are trusted. In this case, the malware was included in the binary which was hosted on Piriform’s server – not on a third-party site.
A similar supply chain attack saw a software update for the Ukrainian accounting application MeDoc compromised. That attack resulted in the download of the NotPetya wiper, which caused billions of dollars of losses for companies.
by titanadmin | Sep 15, 2017 | Email Scams, Phishing & Email Spam, Spam Advice, Spam News, Spam Software |
Consumers should be wary of Equifax phishing scams in the wake of the massive data breach announced earlier this month. The 143 million records potentially stolen in the breach will be monetized, which means many will likely be sold to scammers.
Trend Micro has suggested a batch of data of this scale could easily be sold for $27 million on underground marketplaces and there would be no shortage of individuals happy to pay for the data. The records include the exact types of information that is sought by identity thieves, phishers, and scammers.
However, it is not necessary to have access to the stolen records to pull of scams. Many opportunistic cybercriminals are taking advantage of consumer interest in the breach and are preparing phishing websites to fool the unwary into revealing their sensitive information. Equifax’s response to the breach has also made it easier for phishers to ply their trade.
Equifax has taken the decision not to inform all breach victims by mail. Only the 209,000 individuals whose credit card numbers were exposed will be receiving a breach notification letter in the mail. All the remaining breach victims will have to check the Equifax website to find out if their information was compromised in the breach. With almost half the population affected, and next to no one being directly informed, virtually the entire population of the United States will need to head online to find out if they have been affected by the breach.
Equifax has set up a new domain where information is provided to consumers on the steps they can take to secure their accounts and minimize the risk of financial harm. The official website is equifaxsecurity2017.com. Via this website, U.S consumers can get regular updates and enroll in the free credit monitoring services being offered.
To obtain the free credit monitoring services, consumers will be routed to a website with the domain trustedidpremier.com and will need to enter their name and the last six digits of their social security number to start the process. Cybercriminals have been quick to take advantage and have registered swathes of websites and are using them to phish for sensitive information.
Consumers Should Be Wary of Equifax Phishing Scams
USA Today reports that 194 domains closely resembling the site used by Equifax have already been registered in the past few days. Those domains closely mimic the site used by Equifax, with transposed letters and common typos likely to be made by careless typists. Many of the sites have already been shut down, but more are likely to be registered.
The purpose of these sites is simple. To obtain sensitive information such as names, addresses, Social Security numbers and dates of birth.
The technique is called typosquatting. It is extremely common and very effective. The websites use the same logos and layouts as the genuine sites and they fool many visitors into revealing their sensitive information. Links to the websites are sneaked into malicious adverts displayed via third-party ad networks and are emailed out in large scale phishing campaigns. Consumers should therefore exercise extreme caution and be alert to Equifax phishing scams sent via email and text message.
Consumers should also be careful about revealing sensitive information online and should treat all email attachments and emailed hyperlinks as potentially malicious. Consumers should look for the warning signs of phishing attacks in any email received, especially if it appears to have been sent from Equifax or another credit monitoring bureau, a credit card company, bank or credit union. Email, text messages and telephone scams are likely to be rife following an attack on this scale.
Additionally, all U.S. citizens should closely monitor their credit and bank accounts, Explanation of Benefits Statements, and check their credit reports carefully. Criminals already have access to a large amount of data and will be using that information for identity theft and fraud over the coming days, weeks, months and years.
by titanadmin | Sep 15, 2017 | Industry News, Internet Security, Network Security |
It has been confirmed that poor patch management policies opened the door for hackers and allowed them to gain access to the consumer data stored by the credit monitoring bureau Equifax. The massive Equifax data breach announced earlier this month saw the personal information – including Social Security numbers – of almost half the population of the United States exposed/stolen by hackers.
Poor Patch Management Policies to Blame for Yet Another Major Cyberattack
The vulnerability may have been different to that exploited in the WannaCry ransomware attacks in May, but it was a similar scenario. In the case of WannaCry, a Microsoft Server Message Block vulnerability was exploited, allowing hackers to install WannaCry ransomware.
The vulnerability, tracked as CVE-2017-010, was corrected in March 2017 and a patch was issued to prevent the flaw from being exploited. Two months later, the WannaCry ransomware attacks affected organizations around the world that had not yet applied the patch.
Few details about the Equifax data breach were initially released, with the firm only announcing that access to consumer data was gained via a website application vulnerability. Equifax has now confirmed that access to data was gained by exploiting a vulnerability in Apache Struts, specifically, the Apache Struts vulnerability tracked as CVE-2017-5638.
As with WannaCry, a patch had been released two months before the attack took place. Hackers took advantage of poor patch management policies and exploited the vulnerability to gain access to consumer information.
The Exploited Apache Struts Vulnerability
Apache Struts is used by many Fortune 100 firms and is popular with banks, airlines, governments, and e-commerce stores. Apache Struts is an open-source, MVC framework that allows organizations to create front and back-end Java web applications, such as applications on the public website of Equifax.
The CVE-2017-5638 Apache Struts vulnerability is well known. Details of the vulnerability were published in March 2017 and a patch was issued to correct the flaw. The flaw is relatively easy to exploit, and within three days of the patch being issued, hackers started to exploit the vulnerability and attack web applications that had not been patched.
The remote code execution vulnerability allows an attacker to execute arbitrary code in the context of the affected application. While many organizations acted quickly, for some, applying the patch was not straightforward. The process of upgrading and fixing the flaw can be a difficult and labor-intensive task. Some websites have hundreds of apps that all need to be updated and tested. While it is currently unclear if Equifax was in the process of upgrading the software, two months after the patch had been released, Equifax had still not updated its software. In mid-May, the flaw was exploited by hackers and access was gained to consumer data.
Poor Patch Management Policies Will Lead to Data Breaches
All software contains vulnerabilities that can be exploited. It is just a case of those vulnerabilities being found. Already this year, there have been several vulnerabilities discovered in Apache Struts of varying severity. As soon as new vulnerabilities are discovered, patches are developed to correct the flaws. It is up to organizations to ensure patches are applied promptly to keep their systems and data secure. Had the patch been applied promptly, the breach could have been prevented.
Even though a widely exploited vulnerability was known to exist, Equifax was not only slow to correct the flaw but also failed to detect that a breach had occurred for several weeks. In this case, it would appear that the attackers were throttling down on data exfiltration to avoid detection, although questions will certainly be asked about why it took so long for the Equifax cyberattack to be discovered.
Since zero-day vulnerabilities are often exploited before software developers become aware of flaws and develop patches, organizations – especially those of the size of Equifax – should be using intrusion detection solutions to monitor for abnormal application activity. This will help to ensure any zero-day exploits are rapidly identified and action is taken to limit the severity of any breach.
What Will the Cost of the Equifax Data Breach Be?
The cost of the Equifax data breach will be considerable. State attorneys general are lining up to take action against the credit monitoring bureau for failing prevent the breach. 40 attorneys general have already launched and Massachusetts attorney general Maura Healey has announced the state will be suing Equifax for breaching state laws.
Healey said, the Equifax data breach was “the most egregious data breach we have ever seen. It is as bad as it gets.” New York Attorney General Eric Schneiderman has also spoken out about the breach promising an in-depth investigation to determine whether state laws have been violated. If they have, action will certainly be taken.
U.S. consumers are also extremely angry that their highly sensitive information has been breached, especially since they did not provide their data to Equifax directly. Class-action lawsuits are certain to be launched to recover damages.
As if the breach itself is not bad enough, questions have been raised about the possibility of insider trading. Three Equifax executives allegedly sold $2 million in stock just days after the breach was discovered and before it had been made public.
The final cost of the Equifax data breach will not be known for years to come, although already the firm has lost 35% of its stock value – wiping out around $6 billion. Multiple lawsuits will be filed, there are likely to be heavy fines. The cost of the Equifax breach is therefore certain to be of the order of hundreds of millions. Some experts have suggested a figure of at least 300 million is likely, and possibly considerably more.
by titanadmin | Sep 14, 2017 | Email Scams, Network Security, Phishing & Email Spam, Spam Advice, Spam News, Spam Software |
Cyberattacks on Office 365 users are increasing and Office 365 email security controls are not preventing account compromises at many businesses. If you want to block phishing and malware attacks and prevent costly data breaches, there is no better time than the present to improve Office 365 email security.
Microsoft Office 365 – An Attractive Target for Cybercriminals
Microsoft’s figures suggest there are now more than 70 million active users of Office 365 making it the most widely adopted enterprise cloud service by some distance. 78% of IT decision makers say they have already signed up to Office 365 or plan to do so in 2017 and Microsoft says it is now signing up a further 50,000 small businesses to Office 365 every month. 70% of Fortune 500 companies are already using Office 365 and the number of enterprises transitioning to Office 365 is likely to significantly increase.
Office 365 offers many advantages for businesses but as the number of users grows, the platform becomes and even bigger target for hackers. Hackers are actively seeking flaws in Office 365 and users of the service are increasingly coming under attack. The more users an operating system or service has, the more likely hackers are to concentrate their resources on developing new methods to attack that system.
Cyberattacks on Office 365 are Soaring
Microsoft is well aware of the problem. Its figures show that malware attacks on Office 365 users increased by a staggering 600% last year and a recent survey conducted by Skyhigh Networks showed 71.4% of Office 365 business users have to deal with at least one compromised email account every month. Surveys often overestimate security problems due to having a limited sample size. That is unlikely to be the case here. The survey was conducted on 27 million users of Office 365 and 600 enterprises.
The majority of new malware targets Windows systems simply because there are substantially more users of Windows than Macs. As Apple increases its market share, it becomes more profitable to develop malware to attack MacOS. Consequently, MacOS malware is becoming more common. The same is true for Office 365. More users means successful attacks are much more profitable. If a flaw is found and a new attack method developed, it can be used on millions of users, making searching for flaws and developing exploits well worth the time and effort.
Phishers and hackers are also studying how the security functions of O365 work and are searching for flaws and developing exploits to take advantage. For a few dollars a month, hackers can sign up for accounts to study Office 365. Hackers are also taking advantage of poor password choices to gain access to other users’ accounts to trial their phishing campaigns to ensure they bypass Office 365 email security controls.
Office 365 Email Security Controls are Often Lacking
Given the resources available to Microsoft and its frequent updates, you would expect Office 355 email security to be pretty good. While Office 365 email security is not terrible, for standard users it is not great either. Standard subscriptions include scant security features. To get enhanced security, the enterprise subscription must be purchased or extra email security add-ons must be purchased separately at a not insignificant cost.
Pay for the enterprise subscription and you will get a host of extra security features provided through the Advanced Threat Protection (ATP) security package. This includes message sandboxing, phishing protection, URL tracking and reporting, and link reputation checking. Even when Advanced Threat Protection is used, getting the settings right to maximize protection is not always straightforward.
APT will certainly improve email security, but it is worth bearing in mind that hackers can also sign up for those features and have access to the sandbox. That makes it easier for them to develop campaigns that bypass Office 365 security protections.
Even with both layers of security, the level of protection against malware and phishing is only OK. A 2017 study by SE Labs revealed that even with Microsoft’s Exchange Online Protection and Advanced Threat Protection enabled, email security only achieved a similar score to solutions in the low-middle level of the market. Far lower than the level of protection provided by advanced third party email spam filters such as SpamTitan that work alongside Office 365 to provide even greater protection from malicious email threats.
The Cost of Mitigating an Cybersecurity Incident is Considerable
The cost of mitigating a cyberattack can be considerable, and certainly substantially more than the cost of prevention. The Ponemon Institute/IBM Security 2017 Cost of a Data Breach study shows the average cost of mitigating a cyberattack is $3.62 million.
The recent NotPetya and WannaCry attacks also highlighted the high cost of breach mitigation. The NotPetya attack on Maersk, for example, has been estimated to cost the company up to $300 million, the vast majority of which could have been saved if the patches released by Microsoft in March had been applied promptly.
These large companies can absorb the cost of mitigating cyberattacks to a certain extent, although smaller businesses simply do not have the funds. It is no therefore no surprise that 60% of SMBs end up permanently closing their doors within 6 months of experiencing a cyberattack. Even cash-strapped businesses should be able to afford to improve security to prevent email-based attacks – The most common vector used by cybercriminals to gain access to systems and data.
Increase Office Email 365 Security with a Specialist Email Security Solution
No system can be made totally impervious to hackers and remain usable, but it is possible to improve Office 365 email security and reduce the potential for attacks to an minimal level. To do that, many enterprises are turning to third-party solution providers – specialists in email security – to increase Office 365 email security instead of paying extra for the protection offered by APT.
According to figures from Gartner, an estimated 40% of Microsoft Office 365 deployments will incorporate third-party tools by the end of 2018 with the figure predicted to rise to half of all deployments by 2020.
One of the best ways of improving Office 365 email security is to use an advanced, comprehensive email spam filtering solution developed by a specialist in email security, TitanHQ.
TitanHQ’s SpamTitan offers excellent protection against email-based attacks. The solution has also been developed to perfectly compliment Office 365 to block more attacks and keep inboxes spam and malware free. SpamTitan filters out more than 99.97% of spam and malicious emails, giving businesses the extra level of protection they need. Furthermore, it is also one of the most cost-effective enterprise email security solutions for Office 365 on the market.
SpamTitan Offers Defense In Depth for Office 365 Users
Even with Office 365 Advanced Threat Protection, there are areas where Office 365 does not perform well. According to a study by Osterman Research, Office 365 is capable of blocking all known malware threats. The solution is nowhere near as effective at blocking new malware variants, which are constantly being released. When these new threats are detected and the signatures are added to the database, the threats can be blocked. Until that point, users will be vulnerable. SpamTitan on the other hand is capable of detecting and blocking new malware threats. SpamTitan is able to anticipate new attacks thanks to pattern learning and intelligence. These predictive capabilities ensures protection against the latest malware variants that signature-based email security solutions fail to detect. By using Bayesian analysis, heuristics and machine learning, new types of spear phishing, whaling, and zero day attacks can be detected and blocked that would otherwise be delivered to inboxes.
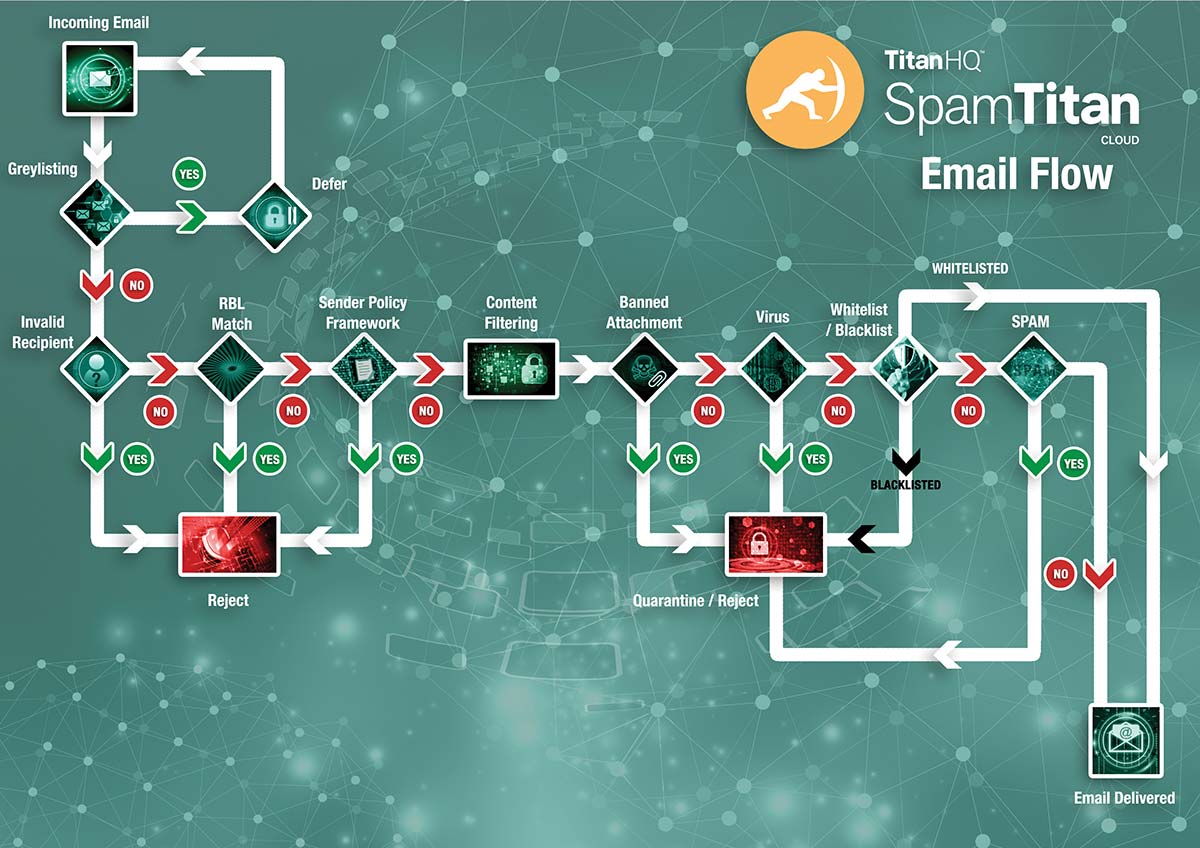
SpamTitan includes URL reputation analysis to assess all embedded hyperlinks in an email, including shortened URLs. SURBL filtering and URL detection mechanisms offer superior protection against malicious links contained in emails. Heuristics are used to identify phishing emails from message headers and are constantly updated to detect the latest emerging threats. SpamTitan also includes a greylisting option. Greylisting involves the rejection of all messages along with a request for the message to be resent. Most email servers respond and redeliver messages quickly. Email servers used for spamming are usually busy and these requests are ignored. This is included as an optional feature in SpamTitan, and can be used in combination with whitelists to ensure trusted senders’ messages are always delivered without any delay. Spam confidence levels can be set by user, user group or domain and the solution integrates with Active Directory and LDAP for easy synchronization.
These combinations of features provide superior protection against phishing, spear phishing, ransomware, malware, BEC, impersonation, and zero-day attacks via email, ensuring businesses are protected and messages do not reach end users’ inboxes.
To find out more about SpamTitan and how it can improve Microsoft Office 365 email security at your business, contact TitanHQ today.
MSPs Can Profit from Providing Additional Office 365 Email Security
The days when MSPs could offer out of the box email services to clients and make big bucks are sadly gone. MSPs can sell Office 365 subscriptions to their clients, but the margins are small and there is little money to be made. However, there are good opportunities for selling support services for MS products and also for providing enhanced email security for Office 365 users.
SpamTitan can be sold as an add-on service to enhance security for clients subscribing to Office 365, and since the solution is easy to implement and has a very low management overhead, it allows MSPs to easily boost monthly revenues.
SpamTitan can also be provided in white label form; ready to accept MSP branding. The solution can even be hosted within an MSPs infrastructure. On top of that, there are generous margins for MSPs.
With SpamTitan it is easy for MSPs to provide valued added service, enhance Office 365 email services, and improve Microsoft Office 365 email security for all customers.
To find out more about how you can partner with SpamTitan and improve Office 365 email security for your customers, contact the MSP Sales team at TitanHQ today.
Vous pouvez lire cet article sur le site TitanHQ.fr.